Top 3 Featured Softwares
List of Top Email Encryption Software


Brevo

Grow with our Email Marketing Platform & CRM suite
Brevo, formerly known as Sendinblue, is a cloud-based marketing and customer relationship management (CRM) platform designed to streamline business communications and drive gro...
View Profile

Moosend

The Easiest Email Marketing and Automation Software
Moosend is an all-in-one email marketing automation software designed to help businesses create, manage, and optimize their email campaigns efficiently. It provides a user-friendly...
View Profile

iContact

Easy email marketing software for your small business
iContact is a powerful email marketing software designed to help businesses create, automate, and optimize email campaigns. It provides user-friendly tools for designing em...
View Profile

Freshmarketer

By Freshmarketer
Freshmarketer is a powerful marketing tool that helps businesses keep up with their ever-changing needs. With Freshmarketer, businesses can run a variety of experiments on their si...
View Profile

Web.com

AI-POWERED WEBSITE BUILDER
Web.Com is an all-in-one website-constructing and business management platform for entrepreneurs, small agencies, and eCommerce proprietors. It affords a smooth-to-use internet sit...
View Profile

Whitevision BV

We know Simplicity
WhiteVision BV is a Dutch software company specializing in automation solutions to streamline and simplify invoice and document management processes. Founded in 2005, the company h...
View Profile

Virtru

By Virtru
Virtru is a tool that provides secure email and attachment protection with end-to-end encryption and advanced controls. The tool has a thoughtful and user-friendly interface, which...
View Profile

NeoCertified

By NeoCertified
NeoCertified is a secure messaging platform that helps companies to send emails through a secure channel without leaving their own browser. The platform can be integrated with Of...
View Profile

Omnisend

Email & SMS marketing so good, it’s boring
Omnisend is a comprehensive marketing automation platform specifically designed for e-commerce businesses to enhance their customer engagement and drive sales through person...
View Profile

Keka HR Payroll Platform

Everything you need to build a great company
Keka HR Payroll Platform is a comprehensive human resources and payroll management software that streamlines employee onboarding, attendance, performance reviews, a...
View Profile

Wrike

One platform to streamline all workflows
Wrike is a powerful cloud-based project management and collaboration software designed to streamline workflows, improve team productivity, and enhance visibility across project...
View Profile
DeliverySlip

By DeliverySlip
DeliverySlip helps to get better security for the files that you share, right from the inbox. You can include attachments of unlimited size from Google Drive, OneDrive, Sharepoi...
View Profile

Telios

By Telios
Telios is a private email service that allows you to securely send and receive end-to-end encrypted emails over a peer-to-peer network. It provides complete ownership of the data...
View Profile

DataMotion Secure Email

By DataMotion Secure Email
DataMotion's SecureMail is a secure way to exchange confidential emails, messages, files, and forms. It uses FIPS 140-2 compliant encryption and has a zero-trust design. It is ea...
View Profile
CTemplar

By CTemplar
CTemplar is an email security management software that offers anonymous, end-to-end encrypted protection to individual users. The software is designed according to the most robus...
View Profile

Xendy

Create and send newsletters in an instant.
Xendy is a user-friendly email marketing platform designed to help businesses create, manage, and optimize their email campaigns efficiently. It offers a seamless experien...
View Profile

Appriver

By Appriver
AppRiver, a Zix company, is a provider of cloud-enabled security and productivity services that focuses on the needs of its channel partners. The company’s brand is built on high...
View Profile

Echoworx

By Echoworx
Echoworx is a customizable email encryption platform that enables companies to deliver protected messages, documents and files, to anyone over any device of their choice. The sol...
View Profile

SendSafely

By SendSafely
SendSafely is a highly secure file sharing platform that allows users to send encrypted files and information to anyone, regardless of the platform. The robust OpenPGP encryption...
View Profile

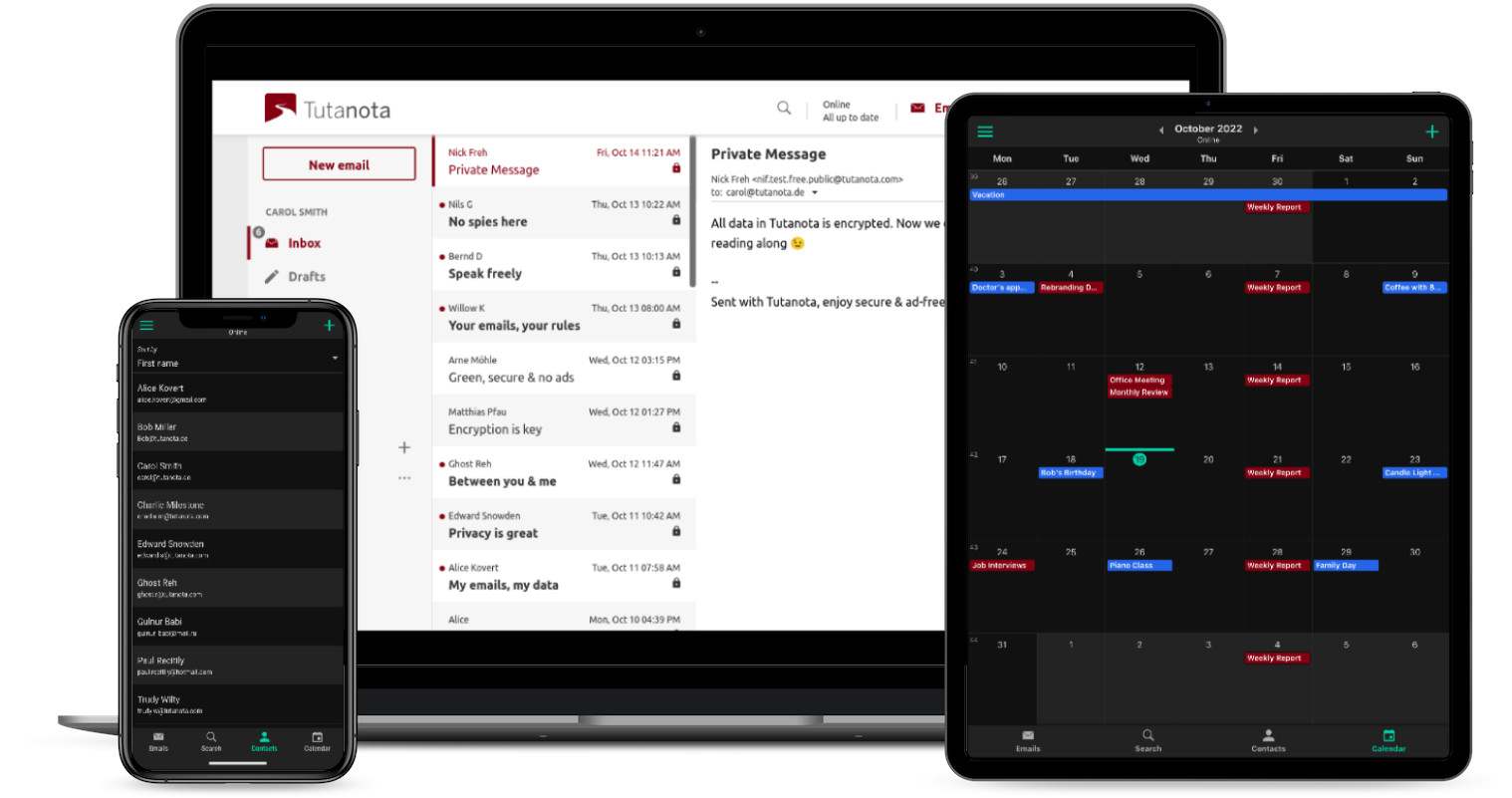
Tutanota

By Tutanota
Tutanota is an end-to-end encryption email service which provides its users with a safer email environment. It has built-in encryption which they guarantee cannot be decrypted by...
View Profile

Table of Content
Selecting the best email encryption software in USA for secure business email communication in a constantly threat-filled digital landscape is a challenge. These tools are often part of broader business email software suites, designed to protect sensitive content via end-to-end message encryption, meaning no unauthorized party can read it. Most modern email encryption software includes compliance capabilities which come enabled to facilitate certain regulatory frameworks, such as HIPAA, GDPR, and CCPA. Additionally, most email encryption programs integrate with existing email platforms and provide advanced features like access controls, message revocation, and real-time threat detection.
1. What is Email Encryption Software?
Email encryption services offer a critical layer of security that protects sensitive communications. Email encryption will scramble your message and turn it into encrypted information (a code) so that only the recipient can read the message. If someone is intercepting the message en route, confidential documents (such as financial reports, medical records, and legal contracts) are secure. Cyber attacks will most assuredly become more rampant with advancing dependency on technologies, and compliance measures set up by legislation such as GDPR or HIPAA necessitate that organizations implement email encryption to continue being compliant and protecting information.
Many firms have begun using integrated email encryption programs that come along with the package of email software for business, and this ensures secure messaging as well as workflow. From a startup utilizing free email encryption software to big organizations making use of the tools at the enterprise grade, encryption is now a baseline requirement in email communication.
2. Criteria for Selecting the Right Email Encryption Software
Choosing the best encrypted email software does not mean getting the highest price one; it means aligning your business requirements with the proper features. Begin an assessment of your existing communication systems. Is integration with Gmail, Microsoft 365, or custom mail servers necessary for setup? Then seamless integration is a must-have. Make sure it works with your existing email marketing software in order to operate smoothly, hasten onboarding, and prevent user errors.
Prioritize compliance, too. Professionals working with strict laws should select tools designed to comply with stringent regulatory demands. Seek configurations that deliver immediate compliance support through built-in HIPAA and GDPR readiness features. Verify whether the software provides straightforward encryption options for users through mechanisms such as one-click features or keyword-based automatic encryption to simplify your team's usage. Usability and scalability are necessary to have. Conduct a final evaluation of available support services alongside documentation quality while checking for included features such as email signature management software, audit trails, and key revocation.
3. Key Concepts of Email Encryption Software
Knowing the basic concepts of email encryption tools enables users to choose their providers wisely. Encryption refers to the whole system, not just one part. It includes some very well-known cryptographic methods to protect email body content, and even attachments and metadata.
-
End-to-End Encryption (E2EE)
Only the sender and receiver can view the email's contents because of end-to-end encryption. No one else, not even the service provider, can read it. Most E2EE systems also have a zero-access design, ensuring that the email platform itself could never have access to your data. E2EE is a good way to ensure your privacy and security with regard to your digital communication.
-
Encryption in Transit
Encryption in transit is a baseline protection for the data that protects the message contents while they are being sent from your devices to your recipient's mail server. Encryption in transit does not provide the same level of strong security as end-to-end encryption, but it is better than sending messages unprotected and is therefore beneficial. Usually done through TLS (Transport Layer Security), it is the standard safety measure available in most email software for business, thereby making it a common baseline for secure communication
-
S/MIME
S/MIME, or Secure/Multipurpose Internet Mail Extensions, is a commonly used standard in business settings. S/MIME uses a digital certificate to encrypt the message and authenticate the sender's identity. If strong encryption and strong identity verification are required, this is great for enterprise-level email encryption programs because S/MIME has native support in many standard platforms such as Outlook and Apple Mail.
-
PGP (Pretty Good Privacy)
PGP is another standard encryption that applies public key cryptography. It can provide quite robust protection but indeed requires more hand management, such as generating keys and exchanging them. PGP happens to be favored by many privacy-oriented individuals and developers, as well as being common in open-source mail encryption software.
-
HIPAA Compliance
U.S. healthcare organizations provide no room for leeway. HIPAA laws strictly implement PHI protection. That implies using encryption software for email with HIPAA-compliant capabilities such as audit trails, access controls, and secure key management. Tools like Paubox and Virtru are known for offering healthcare-ready solutions.
4. Benefits of Using Email Encryption Software
Cybersecurity threats are at an all-time high, and regulations are getting stricter. Email encryption software safeguards personal data, builds trust, and can be used to comply with regulations. The following are important benefits of using encryption software:
1. Privacy and Security
Encryption software hides your emails from prying eyes by encrypting the message content into a code that is unreadable. Only the intended recipients will decrypt it. Companies that share confidential data in any form, including financial information, clients' personal information, or legal papers, will find it extremely useful. Encryption of emails during transmission hugely reduces the potential for data theft, man-in-the-middle attacks, and business espionage.
2. Authentication
Contemporary email encryption programs usually employ digital signatures for authentication of the sender. This disallows spoofing and makes the recipient confident in the source of the email. In business communication—particularly in domains like finance or law—authentication facilitates trust and keeps fraud at bay. It is also very important for establishing secure internal and external workflows among stakeholders. Businesses can improve their security using a combination of email verification software, to check whether or not the email was sent from a valid email address, and email encryption software.
3. Regulatory Compliance
Regulations like GDPR, HIPAA, CCPA, and more put organizations under a duty to care for the safety of any sensitive business or personal information. If not followed, this can lead to large fines and also the loss of reputation. Email encryption software is one means of ensuring compliance, as it enables organizations to obtain secure delivery, tracing, and access control. Certain solutions even include compliance-driven audit logs and reporting capabilities to assist with proving compliance during regulatory audits.
5. How Does Email Encryption Work?
Email encryption follows a technical process of converting plaintext into unreadable ciphertext using complex algorithms often involving key pairs. In asymmetric encryption, which most business-grade solutions use, the sender, therefore, encrypts the message using the recipient's public key. The recipient receives the email and decrypts the message by their private key. This two-key approach is quite secure, even when the public key is made or shared publicly.
More sophisticated email encryption tools integrate with email clients or servers, automatically encrypting messages or according to user-defined rules. Some tools work at the gateway level, encrypting messages as they leave the organization’s mail server. Others are client-based or browser-based. Most contemporary software also includes email testing software functionality to ensure that encryption protocols are correctly engaged before a message is sent, minimizing the likelihood of inadvertent data exposure.
6. What Are the Types of End-to-End Email Encryption Software?
Various email encryption programs provide different approaches to secure information. Encryption types influence security level, user friendliness, and key management. The following are the most common types of encryption used in mail encryption software:
-
Symmetric Encryption
This method uses one key for both encrypting and decrypting the message. It's efficient and quick, hence appropriate for encrypting big files or frequent internal communication. Nonetheless, sharing the key safely between sender and recipient is complicated and poses a security threat. Although not appropriate for external communication, it's applied in some transactional email tools or when used in conjunction with other methods in hybrid applications.
-
Asymmetric Encryption
A public key/private key encryption method will allow a sender and a receiver to maintain secure communication, even if they have never exchanged information previously. The author dispatches a message encoded using the recipient's public key. The secret key of the recipient is the only way to get the message back. Asymmetric encryption forms the basis of contemporary end-to-end email encryption software and is optimal for safe business communication between unknown parties. When combined with Email Tracking Tools, businesses gain not only secure communication but also valuable insights into engagement and delivery.
-
Hybrid Encryption
Most enterprise-level mail encryption software now uses a hybrid approach. The real message itself is encrypted with a symmetric key for speed, and then the symmetric key is encrypted with asymmetric techniques for secure transport. That provides the best of both worlds: the performance of symmetric encryption and the security of asymmetric encryption. Hybrid techniques are particularly beneficial in hosted email encryption solutions where both performance and security are of high priority.
7. Key Features of Email Encryption Software
Modern email management solutions provide features beyond simple security. From access controls to audit logs, these tools help ensure both protection and usability. Here are some features found in top encryption software for email.
1. Revoke Email Access
This allows the sender to view an email that has been sent. For example, if sensitive information is accidentally sent to the wrong recipient, the sender has a way to prevent them from going any further in accessing it. Industries that have constant access to sensitive information like HR, Legal, Finance, and others will surely find it useful, considering that misdelivered information can pose a major problem, just like in the case of a massive data breach.
2. Mail Time-Out
Time-sensitive emails can be programmed to last for a limited amount of time. Then the email becomes unavailable, and sensitive information is safeguarded from potential later misuse. This is great for temporary passwords, confidential bids, or compliance notices. It also supports secure file-sharing practices without leaving long-term exposure windows. Additionally, pairing these features with reliable email finder tools helps ensure that sensitive messages are sent only to verified and accurate addresses, reducing the risk of data leaks or misdelivery.
3. Digital Signatures
A digital signature can let you know that an email is legitimate and has not been modified. They place a cryptographic hash on the communication to show who sent it and if the content has been modified. This can be really helpful in fields like healthcare, law, and finance, where it is necessary by law and for business to check the source of information.
4. Large File Encryption
Some email encryption tools enable secure sharing of large files straight via email without third-party storage sites. It is essential in industries that exchange technical documents, medical images, or high-resolution marketing materials that go over the standard attachment limit. The encryption software, when paired with transactional email tools, makes sure that encrypted file transfers can be automated and personalized. This also makes sure that the critical documents are delivered securely on time.
5. Reporting and Audit Logs
Encrypted secure software generates audit logs, documenting the date and time when the email was opened, who it was opened by, and their IP address. This can help security teams, compliance audits, and incident response understand the logs more easily. If there was a breach, you could check the user's earlier accesses and fix the issue immediately.
6. User-Friendly Interface
Good encryption software should not interrupt workflow. Integration with platforms like Outlook, Gmail, or business email clients, along with drag-and-drop functionality and easy click-to-encrypt capabilities, makes it easier for people to use. Tools with complex interfaces often result in users bypassing encryption—defeating the whole purpose.
8. Common Challenges of Email Encryption Software
While email encryption is critical, it may pose several challenges to organizations, particularly at the time of implementation and scaling. The following are the major issues businesses tend to confront:
1. User Adoption and Usability Issues
Even the most secure email encryption tools can fail if users regard it as too difficult to use. Non-technical staff may steer clear of or misuse the encryption option if it has too many steps or technical terminology. Failure to adopt can create security vulnerabilities, undermining the intentions of encryption altogether. A tool must be simple enough for daily use without requiring constant IT intervention.
2. Platform and Compatibility Limitations
Certain encrypted email software is only compatible with a particular operating system or browser. This becomes a point of tension for organizations that have a diverse technological environment, especially when users are accessing the software through mobile apps or multiple email systems. Incompatibility can result in recipients being unable to decrypt or even access messages.
3. Disruption to Communication Flow
End-to-end encrypted messages usually require receivers to do additional steps, like entering decryption keys or logging into a portal to prove who they are. This lag in accessing messages could mess up workflows, especially when speed is needed, like when legal notices need to be sent, medical issues happen, or clients need to be contacted.
4. Complex Key Management
It takes a long time to manage public and private keys in PGP and S/MIME-based systems. End users often need help from IT staff as they don't know how to safely store, share, and change keys. Poor handling of keys can result in permanent message loss or access failure.
5. Initial Configuration Overhead
Configuring encryption policies, digital certificates, and administrative controls can be a daunting process for IT staff. Things become even more complicated when such functionality is integrated with existing email software for business. Misconfigurations at this point can lead to serious vulnerabilities.
6. Cost and Licensing Constraints
Although there are free email encryption software programs available, most enterprise-level products do have licensing costs that usually vary based on users, storage, or compliance. For small and medium-sized businesses, cost constraints force many to use subpar products or avoid encryption altogether. In the latter case, they open themselves to regulatory risk.
7. False Sense of Security
There is a false sense of security when we rely too heavily on encryption and do not complement it with other security layers, such as phishing/ malware filtering or scanning, sandboxing, etc. Encryption does not guard a person from clicking on a bad link or downloading an infected attachment. A holistic email security strategy is still required.
9. Top 5 Best Email Encryption Software in the USA
1. Tuta
Tuta is a Germany-based, open-source, secure email encryption software popularly used in the USA for its complete end-to-end encryption and ad-free strategy. Tuta encrypts not only subject lines and attachments but also the address book, so it's perfect for privacy-conscious individuals and companies. Its auto-encryption feature prevents users from having to manually activate protection, which is particularly useful for non-tech users.
Features:
-
End-to-end encryption for emails, contacts, and calendar.
-
Encrypts subject lines and metadata.
-
Open-source code for transparency.
-
Secure Connect feature for encrypted contact forms.
-
Custom domains available.
-
Unlimited message sending on the free tier.
Pros:
-
Strong privacy focus (zero-knowledge and no-logs policies).
-
Open-source code allows for auditing.
Cons:
-
Does not support PGP, limiting compatibility.
-
Doesn't offer direct email import.
Pricing: Contains a free plan. Pricing starts at €3.60 /month
2. Virtru
Virtru is an American mail encryption software trusted by enterprises, healthcare, and government institutions. It integrates with Gmail, Outlook, and Google Workspace smoothly, enabling users to encrypt emails within their inbox. Virtru supports client-side encryption and end-to-end encryption software features with excellent control over email forwarding, printing, and expiration.
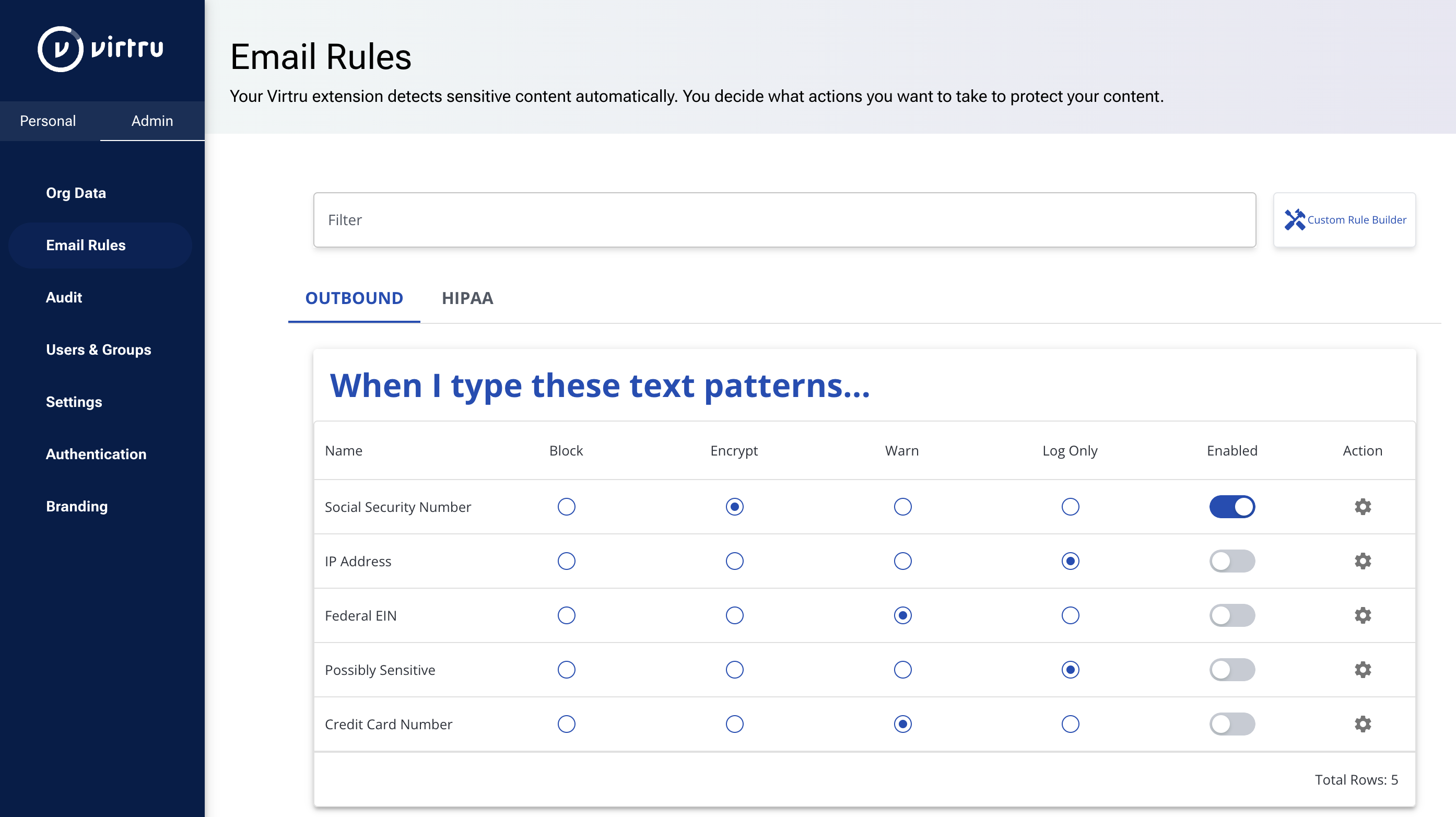
Features:
-
Easy end-to-end encryption for Gmail, Outlook, and other email platforms.
-
Data loss prevention (DLP) capabilities.
-
Email expiration and revocation options.
-
Supports compliance with HIPAA and other regulations.
-
Watermarking of attachments.
Pros:
-
Seamless integration with existing email clients.
-
Allows revocation of sent emails and setting expiration times.
Cons:
-
Recipients may struggle to open encrypted messages, especially on mobile or if not using Virtru.
-
Can be more expensive for smaller teams
Pricing: Pricing starts at $119/month, includes 5 Users
3. Paubox Encrypted Email
Paubox has a hassle-free, zero-click encryption experience, no portals or passwords required for recipients. It is extremely popular in healthcare and finance industries, and completely HIPAA compliant, making it one of the best email encryption software choices for regulatory-heavy industries. In contrast to most tools, it automatically encrypts emails, even those sent to recipients outside the system.
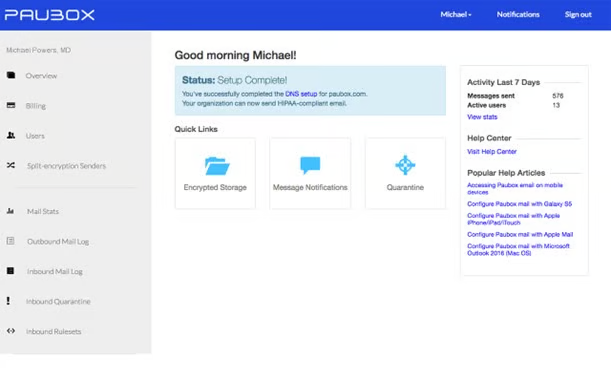
Features:
-
Automatic, seamless encryption of all inbound and outbound emails.
-
Inbound email filtering
-
No need for plugins or portals.
-
Provides a Business Associate Agreement (BAA) for HIPAA compliance.
-
Includes anti-spam and anti-virus features.
Pros:
-
Very easy to use for both senders and recipients.
-
Strong focus on HIPAA compliance.
Cons:
-
No end-to-end encryption on internal emails
-
No free tier available, minimum user requirement for plans.
Pricing: Pricing starts at $29/mo 1 senders
4. SecureMyEmail
SecureMyEmail is a small business and consumer-friendly software that can be used with most email services, making it a versatile encryption software for email. It implements PGP encryption but strips away the technical difficulties, providing a sleek and easy-to-use interface on devices. The application also offers encrypted cloud storage for the sent emails, making it one of the Best email archive software options for businesses and individuals seeking secure retention.
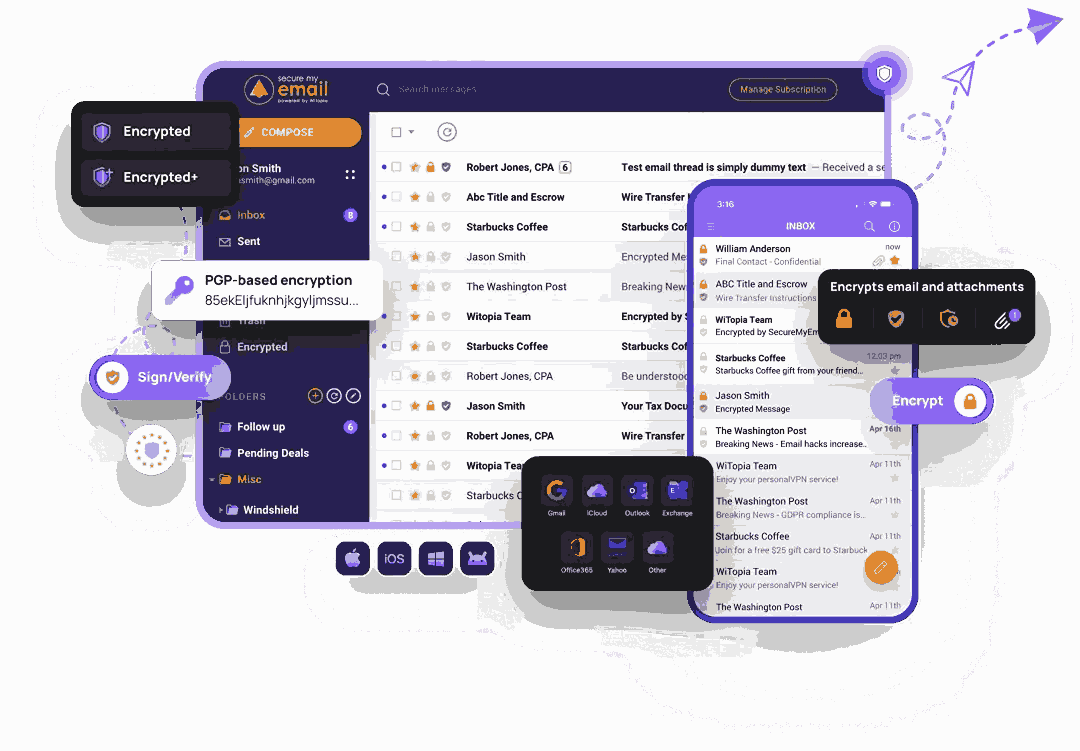
Features:
-
Encrypts emails from existing accounts using IMAP support.
-
Supports existing PGP keys for encryption.
-
Multi-factor authentication (MFA) available.
-
Adjustable message expiry times.
-
encrypted cloud archive
Pros:
-
Allows users to retain their existing email addresses.
-
Offers a feature-complete free tier.
Cons:
-
Lacks deep integrations for enterprise environments,
-
Password-based encryption for non-users is less secure.
Pricing: The pricing starts at $12.99/month for a 1-month subscription
5. PreVeil
PreVeil offers enterprise-grade end-to-end encryption software that balances ease of use with high-quality security. Based on zero-trust architecture, it is optimized for secure file exchange and encrypted email correspondence between companies and contractors. PreVeil helps ensure compliance with ITAR, DFARS, and CMMC, all important when dealing with the U.S. Department of Defense.
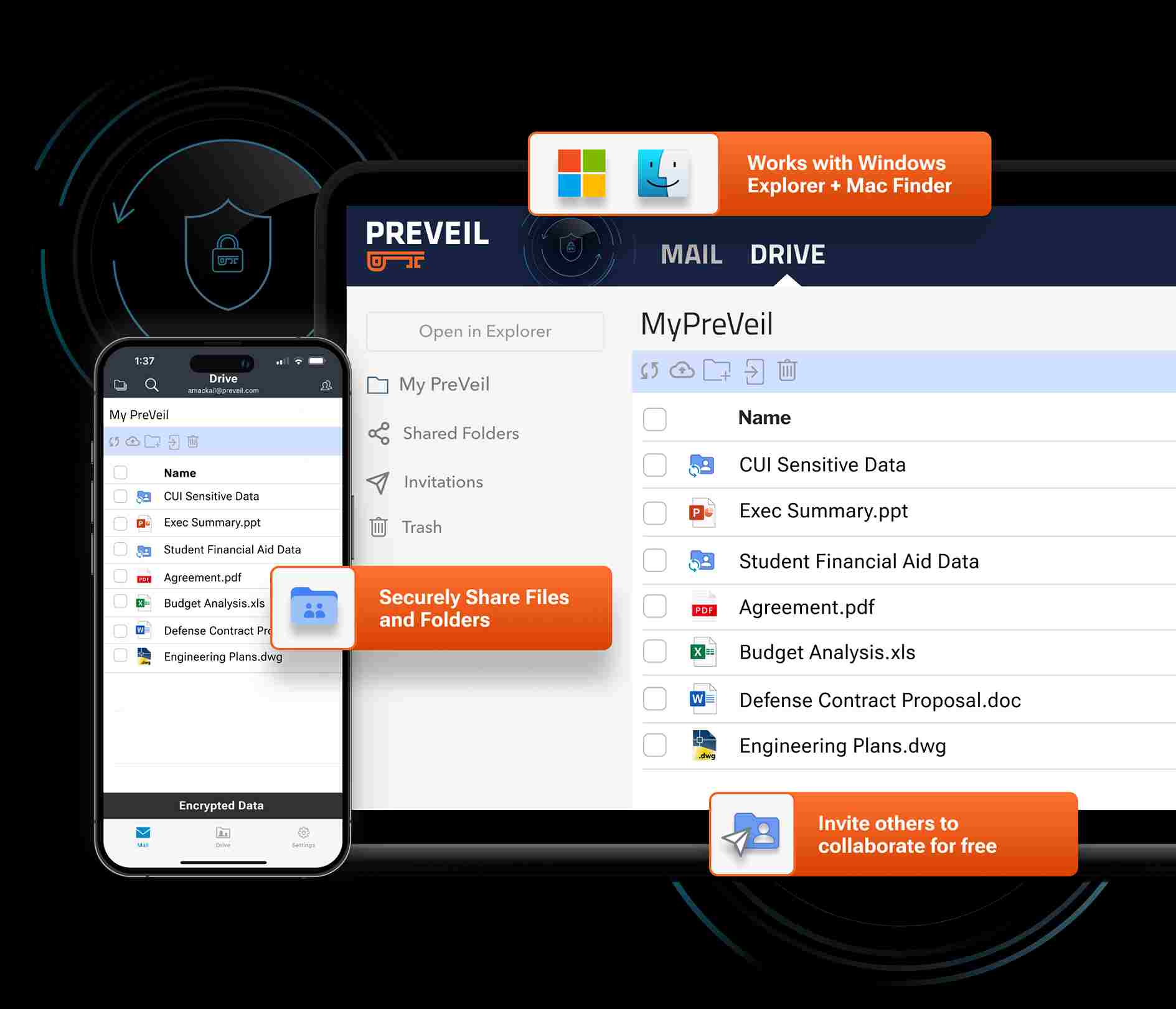
Features:
-
End-to-end encryption for email and files.
-
Access revocation
-
Encrypted cloud storage
-
Enterprise key management.
-
shared email inboxes
Pros:
-
Defense-grade security
-
great for compliance-heavy sectors
Cons:
-
Requires manual installation on unsupported email clients
-
Requires onboarding for non-tech-savvy users
Pricing: Pricing starts at $25/ Month
10. Latest Market Trends in Best Email Encryption Software
As the world becomes increasingly reliant on technology, cyber threats are rising in parallel, making strong email encryption software more essential than ever for protecting sensitive communications. According to the market overview given by the Market Research Future, the Email Encryption Market is expected to grow at a rate of 22.96% per year, rising from USD 4.93 billion in 2024 to USD 25.8 billion by 2032. Moreover, the Email Encryption market was worth USD 3.9 billion in 2023. Below are some of the latest market trends driving change in today’s best Email Encryption Software.
1. AI-Powered Threat Detection
Email encryption is no longer just about scrambling data — it's also about predicting and preventing attacks. Advanced email encryption tools are increasingly integrating AI and machine learning to detect suspicious patterns in communication. These systems can spot phishing, spoofing, and data leakage attempts in real time, even before emails are opened. This proactive security model enhances traditional encryption by reducing human error, which remains a major vulnerability in email systems.
2. Homomorphic Encryption
Arguably, the most groundbreaking development, homomorphic encryption, makes it possible to process and analyze data without decrypting it. In email security, that means sensitive information can be searched, scanned, or filtered without ever being exposed. Though in the infant stages now, it is likely to become increasingly common in enterprise mail encryption software as it holds both privacy and productivity together without sacrificing either.
3. Enhanced User Experience
One significant barrier to encrypted email software adoption has been convenience. In recent times, there is a clear trend toward user-friendly interfaces that simplify setup, access, and reading of encrypted emails. Zero-click decryption, key management, and help tools built into the software are becoming simpler to use for senders and receivers alike. Making it simpler is essential for companies wanting to protect communication without overwhelming staff or clients.
4. Integration with Other Security Solutions
Today's encryption solutions are no longer standalone products. Leading providers now offer integration with other cybersecurity solutions such as endpoint security, SIEM systems, and Data Loss Prevention (DLP) products. This move toward a converged security stack enables organizations to control encryption, monitoring, and threat analysis from a unified dashboard, enhancing visibility, control, and operational efficiency.
5. Cloud-Based Solutions
With SaaS and remote work in widespread use, cloud-based email encryption software is in huge demand. Such tools are easily deployable, automatically update, and scale without causing heavy capital expenditures. Hosted encryption products are especially attractive to start-ups, SMEs, and blended workplaces seeking nimble protection without taxing IT infrastructure.
6. Compliance-Driven Adoption
Stringent data protection laws such as GDPR, HIPAA, CCPA, and India's DPDP Act are propelling an increase in the adoption of email encryption software. Firms now consider encryption not only a security best practice but also a law necessity. Solutions that provide compliance-specific templates, audit trails, and automated reporting capabilities are particularly sought after by healthcare, legal, and financial services organizations.
7. Quantum-Safe Security
As quantum computing has become a reality, there is a rising concern that existing encryption standards will be rendered out of date. Top vendors are gearing up by creating quantum-resistant encryption algorithms, rendering their email software for business ready for the future. While mass implementation is still a matter of a few years, quantum-safe readiness is already a strategic priority on the agenda for most enterprise security teams.
11. Conclusion
In today's digital world, it is crucial to choose the right email encryption software for business in order to protect sensitive communications and ensure compliance with regulations. Modern email encryption software not only protects your privacy, but mit supports seamless integration, advanced features, and ease of use. By selecting a trusted provider, businesses can ensure secure, reliable, and regulation-ready communication at every level.

 Researched and Written by
Researched and Written by