Top 3 Featured Softwares
List of Top Customer Identity And Access Management (CIAM) Software


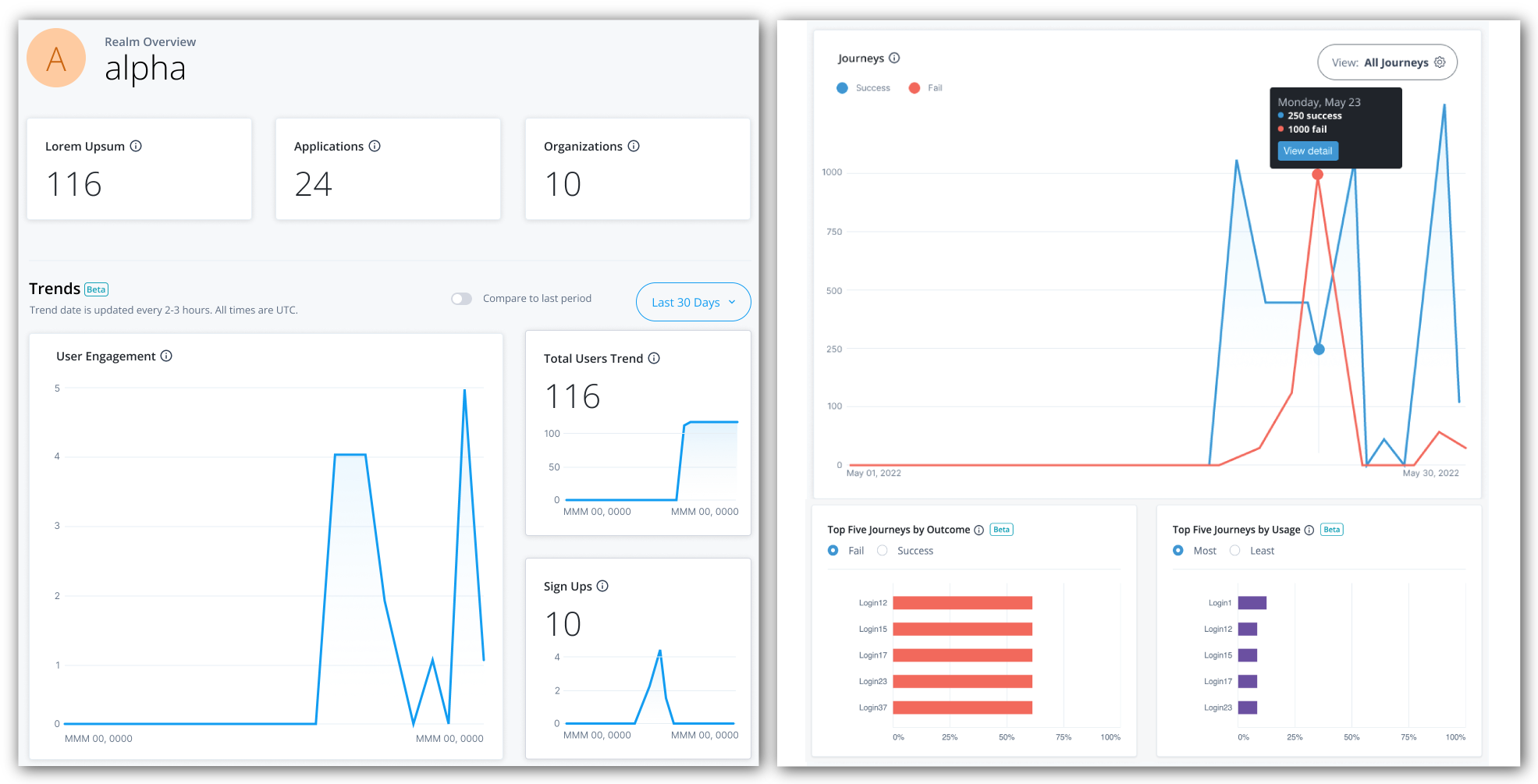
Auth0

By Auth0
Auth0 is a software that provides a platform for organisations to authenticate and authorize management policies that function and can be accessed through the web, IoT, mobile ha...
View Profile

SecZetta Customer Identity

By SecZetta Customer Identity
SecZetta's NE Profile and NE Access products provide a complete solution for managing customer identities across all of these channels. SecZetta's NE Profile and NE Access produc...
View Profile

miniOrange Single Sign-On

By miniOrange Single Sign-On
MiniOrange Single Sign-On is a modern solution that allows users to create a single set of login credentials to access multiple applications. This platform not only saves time by p...
View Profile

Persona

By Persona
Support multiple types of ID documents from over 200 countries, including passports, driver's licences, and ID cards. The software is available in 14 languages. Persona is an ide...
View Profile
Userfront

By Userfront
Userfront is a customer identity and access management software that provides secure, standards-based authorization services. They have a simple setup and provide automatic updat...
View Profile

Tappd(in) Community Bundle

By Tappd(in) Community Bundle
. A mobile app that can be configured, a digital wallet, and a consent-based access control server work together to provide digital experiences that respect privacy.
View Profile

Sphere Identity

By Sphere Identity
Sphere Identity is a global identity provider that helps businesses and individuals protect their information. It is built on the principles of Privacy-by-Design, which means tha...
View Profile

ClearDil

By ClearDil
As the industry leader in identity verification and authentication, ClearDil offers businesses superior security with its up-to-date, risk-based approach. With regular global AML...
View Profile

ReachFive

By ReachFive
ReachFive is a Customer Identity and Access Management (CIAM) platform that helps companies to create unique customer experiences. The platform helps users to authenticate their ...
View Profile

Sentry Login

By Sentry Login
Sentry Login is compatible with Weebly, Squarespace, Yola, WordPress, Blogger, Yahoo Sitebuilder, GoDaddy, Webflow, Adobe Muse, and any other system that does not use iFrames. It...
View Profile

OneWelcome

By OneWelcome
Welcome to OneWelcome, the result of a collaboration between two Dutch SaaS businesses, iWelcome, and Onegini. Our CIAM (customer identification and access management) program ma...
View Profile

Frontegg

By Frontegg
Frontegg provides extensive user management capabilities for B2B SaaS applications, supporting a self-service experience for your customers. Frontegg can handle everything from s...
View Profile

Akamai Identity Cloud

By Akamai Identity Cloud
Akamai Identity Cloud is a customer identity and access management solution that enables businesses to create a personalised customer experience inclusive of proper security feat...
View Profile

Simeio

By Simeio
Simeio is a comprehensive IAM (Identity and Access Management) solution that is unrivaled in its "service first" mindset. It interacts securely with everyone, anywhere, at any ti...
View Profile

Amazon Cognito

By Amazon Cognito
Amazon Cognito is a web service that controls user authentication and access for mobile applications on internet-connected devices. It allows simple and secure user authenticatio...
View Profile

Ubisecure CIAM

By Ubisecure CIAM
Ubisecure CIAM is a customer identity and access management software that can be used to offer registration as a Service to individual users. Thus facilitating a standard login e...
View Profile

LoginRadius

By LoginRadius
LoginRadius is an enterprise-grade cloud-based customer identity and access management platform that empowers and upgrades businesses in providing a wonderful customer experience...
View Profile

FusionAuth

By FusionAuth
FusionAuth is a comprehensive user management tool that extends its capabilities beyond just that. Getting started and setting up the tool happens in minutes as it is compatible ...
View Profile

Saviynt
By SaviyntCheck How Saviynt can help to automate Indian Business. SaaSAdviser provide their list of features, pricing, Free demo and Comparison with the best alternative
View Profile

OneLogin

By OneLogin
OneLogin is a compact value identity and access management software trusted by 2000+ customers all over the globe. It provides resource optimization, top-graded operational efficie...
View Profile

Table of Content
What is Customer Identity and Access Management (CIAM) Software?
Customer Identity and Access Management (CIAM) software is an expert form of Identity and Access Management (IAM) that deals with the digital identity of your external users, who are your customers. Unlike the traditional IAM that processes employees (the workforce), CIAM solutions are designed to support millions of identities, provide frictionless user experiences, and offer high data privacy standards and regulations.
The main constituent of CIAM software is the system that controls the whole customer identity lifecycle, including the registration and login procedure, profile administration, consent, and eventual deletion. It offers the tools and services needed, like the Single Sign-On (SSO), Multi-Factor Authentication (MFA), and social login to ensure that the customer data stays safe, and at the same time, the user experience is not inconvenienced to an extent that requires additional time.
This CIAM technology is aimed at achieving two purposes: to secure your applications and websites from threats, as well as to build a personalized, seamless, and unified experience that makes customers come back. Once implemented in the right way, your Customer Identity and Access Management Platform is a security and business growth engine.
1. Why Businesses Need Customer Identity and Access Management (CIAM) Software
The online environment, with its multifaceted laws on data protection and advanced hacking, needs a specific CIAM platform. The powerful CIAM solutions are essential investments that offer very important benefits in security, compliance, and customer experience.
1. Enhanced Security and Fraud Prevention
There are always digital threats such as account takeover (ATO), credential stuffing, and bot attacks. CIAM software enables highly developed authentication and authorization functions, which significantly decrease the risk of such breaches. Such features as adaptive MFA and risk-based authentication are applied to make sure that access is provided when the context of the user is checked to protect the customer and the enterprise.
2. Scalability for Millions of Users
The number of workforce IAM may deal with is thousands of employees, whereas a successful digital product can lure millions of clients all over the world. CIAM platforms are designed to be of enormous scale and can handle peak registration and login traffic without causing performance degradation.
3. Frictionless Customer Experience (CX)
An awkward registration or log-in checkout is a significant deterrent to conversion. Customers demand the comfort of social login and the convenience of Single Sign-On (SSO). An adequately installed customer identity and access management software will decrease friction in the form of a log-in, decrease the cart abandonment rate, and increase customer satisfaction and retention.
4. Compliance with Global Regulations
Laws such as GDPR, CCPA, and HIPAA contain stringent directives regarding the process of collecting, storing, and processing customer data. Consent management, sound data governance, and audit logging are key functionalities of CIAM solutions that are essential in proving compliance and evading huge regulatory fines. This attention to the customer identity and access control solutions to compliance is a significant contrast to the conventional IAM.
2. Steps to Select the Customer Identity and Access Management (CIAM) Software
The selection of the appropriate CIAM software is a strategic move that ought to be done with due diligence. A systematic process will make sure you choose a platform that supports your future business objectives and present goals.
1. Define Your Needs
Begin by properly recording what you need.
-
Scale and Volume: What is the number of active users you have now, and how many in the next three to five years? This will automatically reduce your list of viable vendors of CIAM.
-
Define Strengths: What are the must-have authentication methods (e.g., social, passwordless)? Do you need advanced B2B, such as delegated administration?
-
Visualize the User Journey: Map out all the areas of interaction involving identity, including guest checkout, profile updates, etc. The CIAM solution needs to improve every stage of this process.
2. Compare Vendors
Acquire information and analyze available CIAM providers depending on the core services.
-
Comparison of Market Reputation: Seek Gartner Magic Quadrant or Forrester Wave reports, but only those that are acknowledged as CIAM platform leaders. Reviews of sites such as G2 and Capterra determine the level of satisfaction of customers with the product and support.
-
Assess Feature Depth: Do not simply tick a box. Explore the maturity of major capabilities such as adaptive MFA, API security, and identity orchestration of all analyzed CIAM software.
-
Examine Deployment Flexibility: Does your organization need a fully cloud-native platform, or does it need a hybrid architecture that will connect with the existing on-premises resources? This is important to the platform being flexible.
3. Test Security & Usability
A CIAM system must provide the right balance between customer security and customer usability.
-
Security Testing: Demand certain information on security certifications (e.g, ISO 27001, SOC 2) and identify threats by the vendor. A Proof of Concept (PoC) should be conducted to test risk-based policies.
-
Usability Review: Use a non-technical group of users to test the registration, the login, and the profile management flows. High conversion rates imply that conversion is low, no matter how safe the system is.
-
Developer Experience: These are because your development team will incorporate this CIAM technology and consider the quality of SDKs, APIs, and documentation. An excellent developer experience accelerates time-to-market.
4. Assess Integration
A customer identity and access management platform is not a vacuum but requires interoperability with your existing technology stack.
-
Ecosystem Compatibility: Make sure that the CIAM software is pre-integrated with your CRM (e.g., Salesforce), marketing automation software (e.g., Marketo), and analytics software.
-
Quality of API: API is the most important factor, and the quality of the vendor API and its strength are enormous, and you can integrate it deeply and customize it with your mobile and web applications.
-
Orchestration Capabilities: Does the CIAM solution have the capability of orchestrating with other security controls, like fraud detection services or bot mitigation solutions, with low-code or no-code orchestration?
5. Make Data-Driven Decisions
The last selection must be done under measurable metrics.
-
Total Cost of Ownership (TCO): Is there more than the cost per user? Include implementation expenses, system maintenance, support charges, and labor inside the organization to administer the CIAM identity management system.
-
Performance Metrics: The vendor must make promises of service level agreement (SLA) of uptime and latency, particularly during events of high traffic. Quick response rates have a direct influence on the customer experience.
-
Future Roadmap: Select a CIAM vendor whose roadmap is clear and ambitious and is in line with future trends, including decentralized identity and additional AI-driven security innovation.
3. Features of Customer Identity and Access Management (CIAM) Software
The best customer identity and access control software offers a full package of functionalities that cater to all the requirements of the customers and developers, as well as the security administrators.
1. User Authentication Methods
Customer Identity and Access Management Solutions provide various authentication systems such as MFA, biometrics, and passwordless authentication to provide a higher level of security. CIAM technology provides platform-adaptive authentication through frictionless yet secure access. It also incorporates the best single sign-on software to allow one integrated, and smooth user experience.
2. Identity Verification
CIAM Customer Identity and Access Management software is used to verify the identities of users by scanning documents or verifying through biometrics and OTP. Such systems guarantee actual customer onboarding and lower risk of fraud. CIAM Identity Management enhances confidence and protection in the digital medium.
3. Data Privacy & Compliance
The contemporary CIAM technology complies with such international standards as GDPR, CCPA, and HIPAA. It offers verifiable consent management and information sovereignty. CIAM is one of the top compliance management software companies, and it provides full compliance with the regulations.
4. Scalability & Performance
The customer identity and access management solutions can manage millions of people using them simultaneously. They are web-based and have high performance and scaling. Ciam technology encourages expansion without affecting the security or reliability.
5. APIs & Integrations
CIAM Identity Management can integrate with CRM, ERP, and marketing platforms with secure APIs. Such integrations make user management easy, and the workflow is automated. It is in favor of the best commercial unified identity services for enterprise flexibility.
6. Self-Service Options
CIAM Customer Identity and Access Management solutions are based on self-registration, a password, and updating a profile. This saves on administration and increases user control. It enhances customer satisfaction, and security is maintained.
7. Security Features
CIAM technology is advanced and provides adaptive MFA, encryption, and behavioral analytics. It goes hand-in-hand with privileged access management solutions of secure role-based control. In real time, breaches are prevented through access monitoring and anomaly detection.
8. Analytics & Reporting
CIAM Identity Management offers information about the user behavior, access patterns, and security threats. It has an auditing and compliance dashboard. These analytics are combined with Access Governance Software Applications in the process of informed decision-making.
4. Benefits of Customer Identity and Access Management (CIAM) Software
Implementing a robust CIAM solution will provide value that cuts across almost all organizational areas, including IT protection, marketing, and sales.
1. Improved Security
CIAM enhances data security through the use of adaptive MFA, encryption, and ongoing threat monitoring. It helps to minimize the chances of identity theft and unauthorized access. This keeps the accounts of customers safe on all online touchpoints.
2. Frictionless Customer Experience
CIAM allows the use of SSO and social logins as well as passwordless authentication. It reduces obstacles to registration and access. This brings about increased satisfaction and fewer user drop-offs.
3. Trust & Compliance
CIAM regulates privacy legislation, such as GDPR and CCP, through consent management. It offers transparency in data manipulation and control by the user. Established trust leads to customer relationships in the long term.
4. Personalization
CIAM facilitates interaction by creating a single customer data to allow customization of interactions across channels. It assists in the personalization of experience by preference and behavior. This leads to involvement and brand loyalty.
5. Business Growth
CIAM simplifies the onboarding process and increases the conversion rates. It facilitates the expansion of customer bases safely. The closer customer relations lead to the increase in revenues.
5. Top 5 Customer Identity and Access Management (CIAM) Software Providers in the USA
There are a few key CIAM vendors dominating the market, with each having a strength in the customer identity platform and access management software market. The following table compares five of the leading CIAM vendors in the US market.
1. Okta – Secure Identity, Seamless Access.
Okta, and especially its Customer Identity product (with the Auth0 platform), is a major cloud-native vendor of CIAM and has a rich and developer-centric integration ecosystem. The solution offered by Okta is a workforce and customer identity management solution that will be a part of one solution; that is why it would be an appealing solution to be employed in the organizations in need of an all-encompassing CIAM solution.
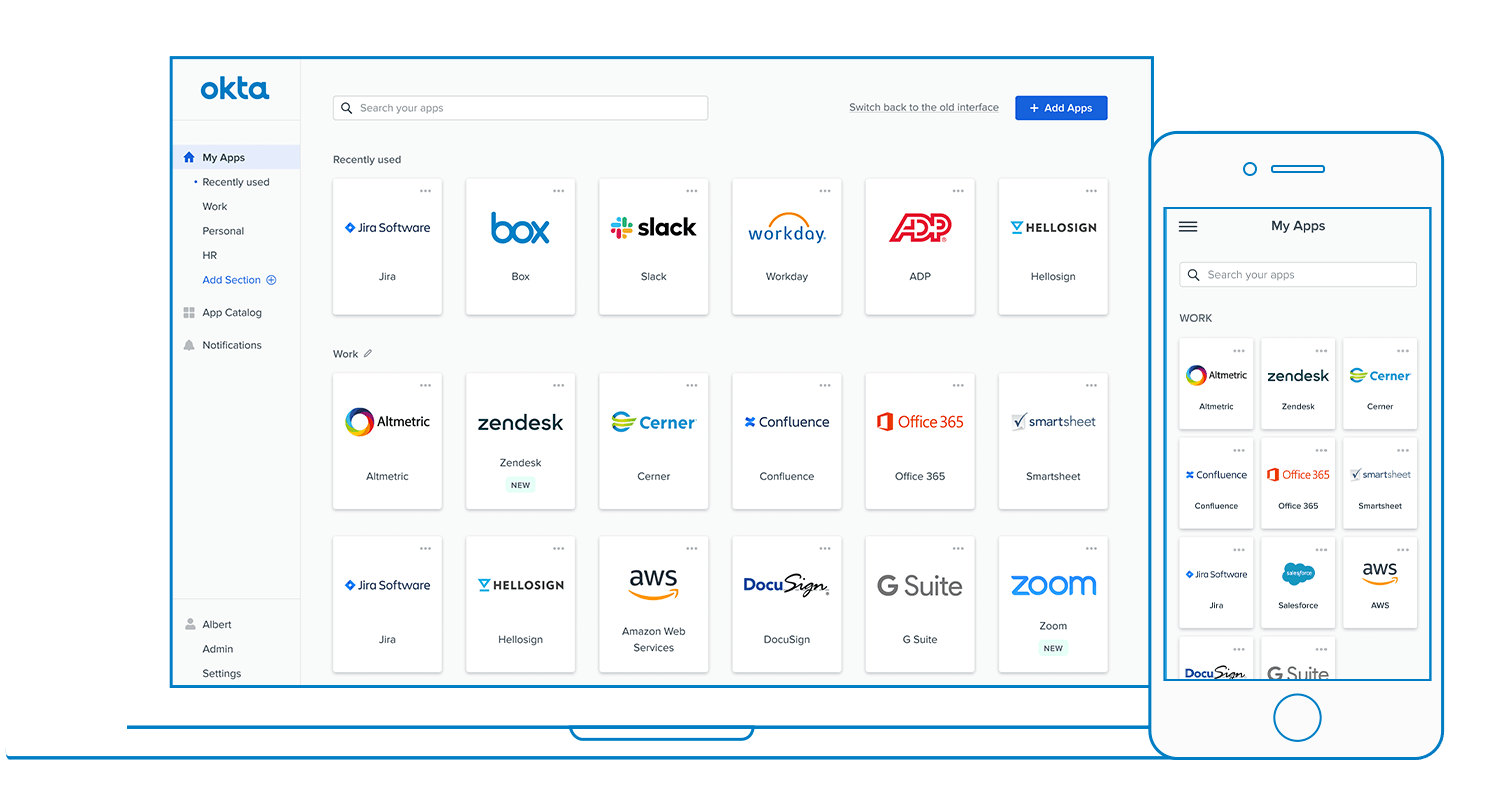
Features:
-
Single Sign-On (SSO) for cloud and on-prem apps.
-
Adaptive Multi-Factor Authentication (MFA).
-
Universal Directory for centralized identity management.
-
Lifecycle management for user onboarding/offboarding.
-
API Access Management for secure integrations.
Pros:
-
Easy to integrate with thousands of apps.
-
Scalable and cloud-native.
-
Strong security and compliance features.
Cons:
-
Higher cost for small businesses.
-
Advanced setup requires technical expertise.
-
Pricing structure can be complex.
Pricing: Starts at around $35/month.
2. Ping Identity – Intelligent Identity, Trusted Access.
Ping Identity is an old and reputable CIAM vendor and is preferred especially by large companies and organizations in regulated industries that demand a flexible approach of both cloud and on-premise deployments. They give much attention to smart and risky access.
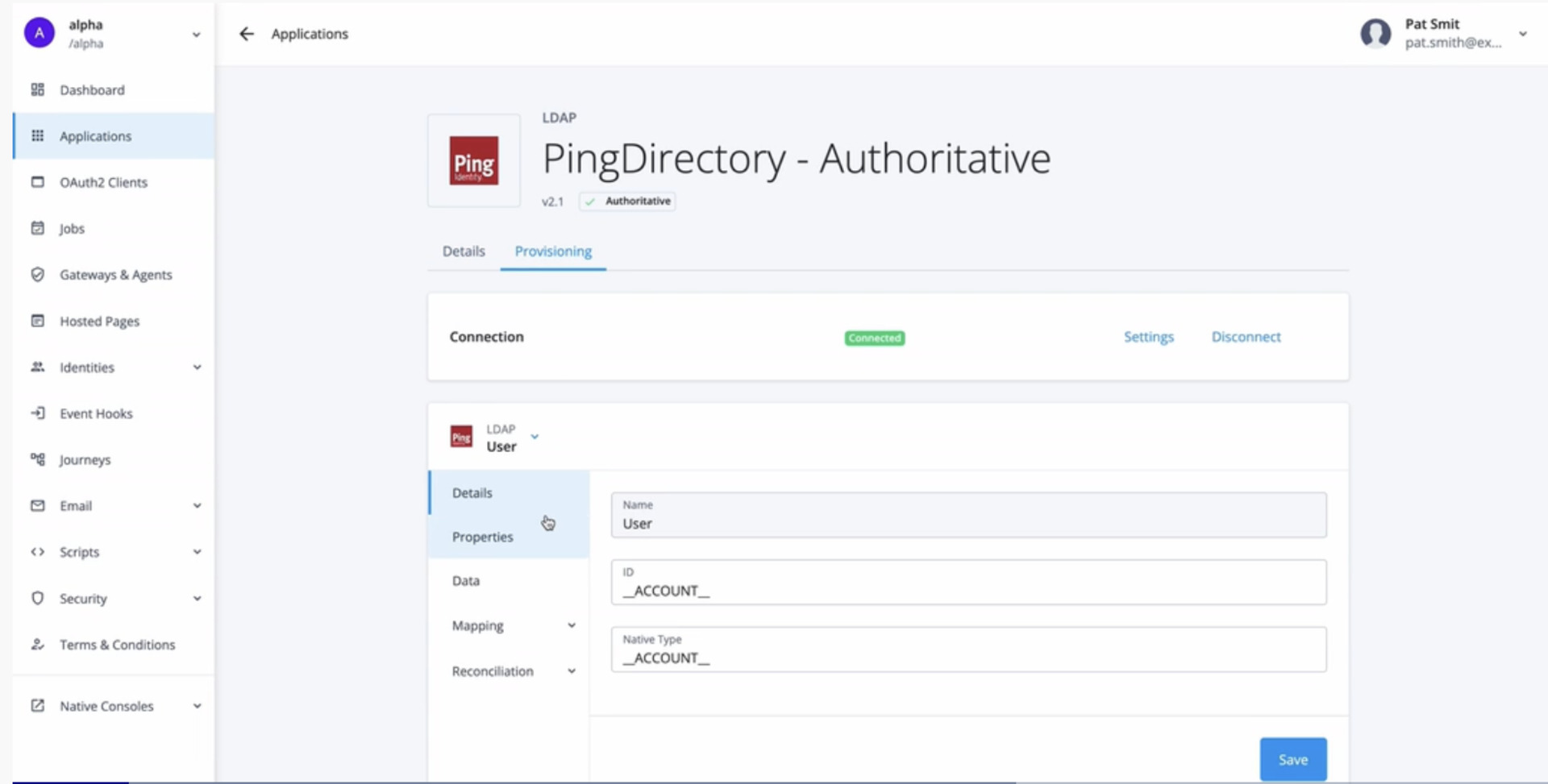
Features:
-
No-code identity orchestration workflows.
-
SSO and adaptive MFA support.
-
API security and access management.
-
Passwordless authentication.
-
Integration for customer and workforce identity.
Pros:
-
Highly customizable and flexible.
-
Excellent standards support (SAML, OIDC).
-
Good hybrid and enterprise integration.
Cons:
-
Expensive for smaller organizations.
-
Complex to implement.
-
Requires experienced admin setup.
Pricing: The plan starts at $35k annually.
3. Microsoft Entra ID – “Empowering Secure Connections Everywhere.”
The natural first option is Microsoft Entra ID (previously Azure Active Directory) in case an organization engages in the Microsoft ecosystem on a large scale. Being a cloud identity service, it has developed into a full-fledged CIAM software, especially in B2C applications, and external cooperation (B2B).
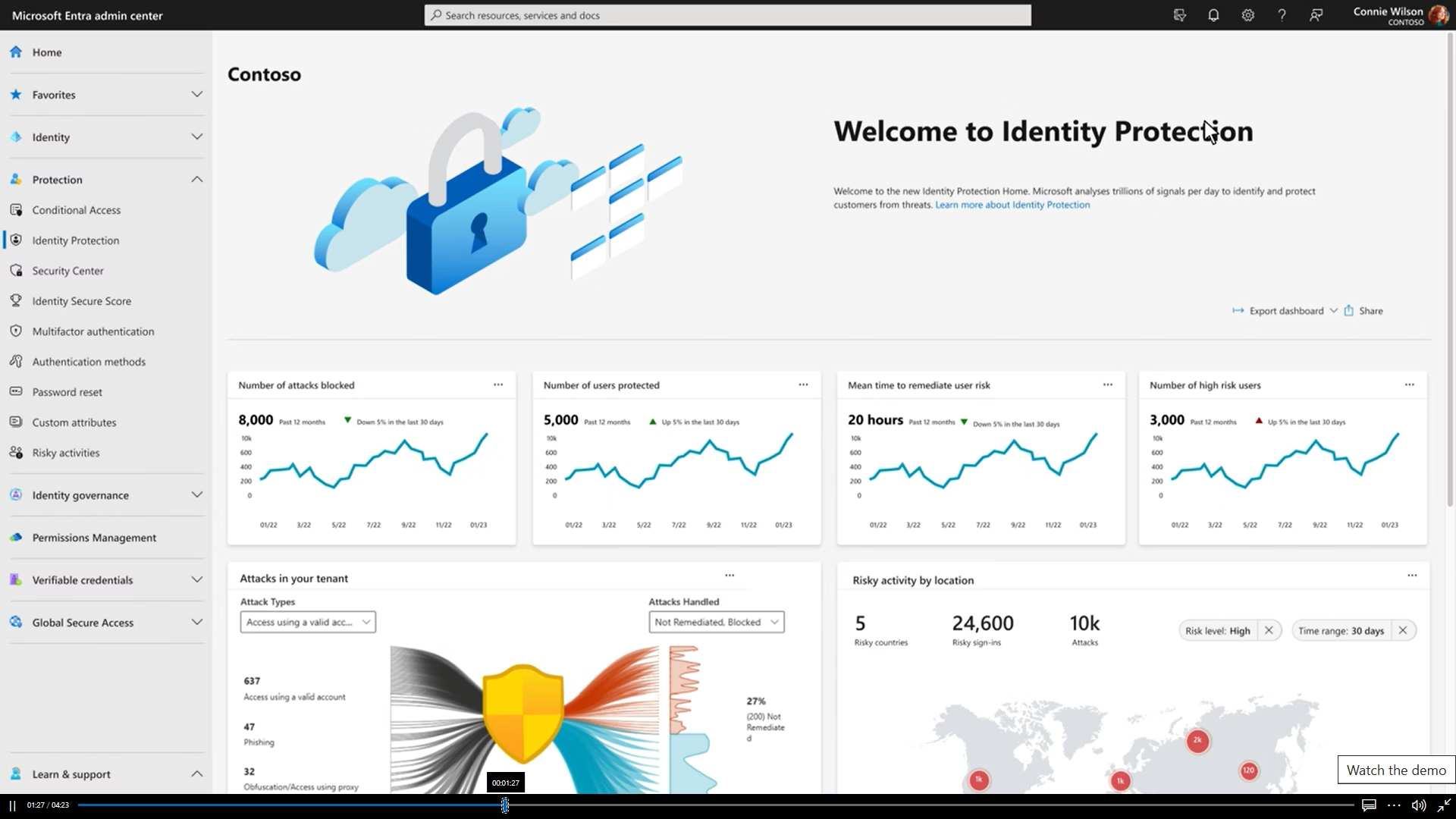
Features:
-
Centralized identity for Microsoft 365 and Azure.
-
Conditional access and risk-based policies.
-
Passwordless sign-in and MFA.
-
Privileged Identity Management (PIM).
-
External and workload identity support.
Pros:
-
Deep integration with the Microsoft ecosystem.
-
Cost-effective for Microsoft users.
-
Scalable and reliable cloud identity service.
Cons:
-
Limited appeal for non-Microsoft environments.
-
Complex licensing tiers.
-
Some advanced tools require higher plans.
Pricing: The plan starts at $6.00/month.
4. ForgeRock – Flexible Identity, Enterprise Confidence.
ForgeRock (since acquired by Ping Identity) is an upscale, highly customizable CIAM vendor, traditional in attracting enormously large, complex organizations that need very high flexibility and control in their identity deployments. It has been known to have the capability of dealing with very large-scale and complicated customization.
Features:
-
Drag-and-drop identity orchestration.
-
Multi-cloud and on-prem deployment options.
-
Adaptive authentication and risk analysis.
-
Directory services and provisioning.
-
IoT and customer identity support.
Pros:
-
Highly customizable enterprise platform.
-
Strong scalability and orchestration.
-
Supports diverse identity types.
Cons:
-
Complex to deploy and maintain.
-
Expensive for smaller teams.
-
Requires technical expertise.
Pricing: Visit the website for detailed pricing.
5. IBM Security – Protecting Identities, Ensuring Compliance.
Using its IBM Security Verify suite, IBM Security uses the massive knowledge and AI capacity of IBM to provide an all-encompassing, enterprise-scale CIAM platform. It specifically succeeds well in strictly governed and high-volume settings where control and complex analytics are central factors of concern.
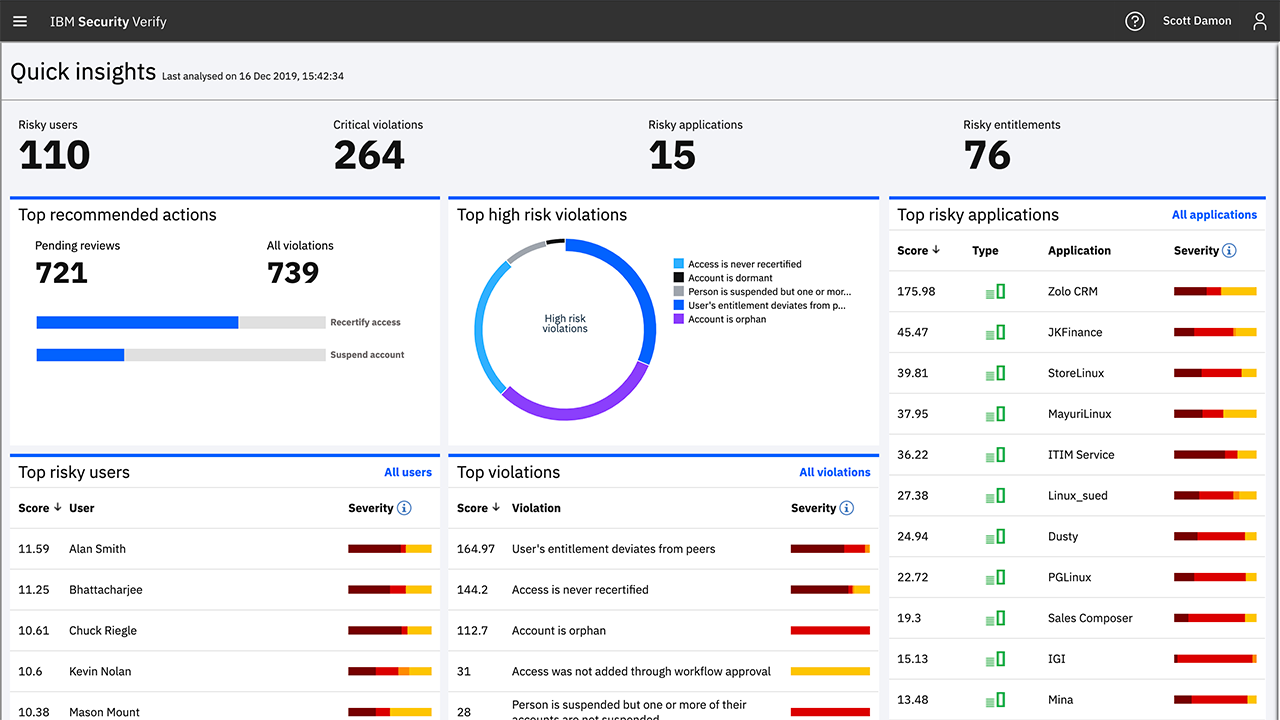
Features:
-
SSO and adaptive MFA.
-
Identity governance and compliance tools.
-
Lifecycle management and provisioning.
-
Risk-based access controls.
-
Cloud and hybrid deployment support.
Pros:
-
Comprehensive compliance and governance features.
-
Strong enterprise support and integrations.
-
Highly scalable.
Cons:
-
Complex pricing and licensing.
-
Requires technical configuration.
-
Less user-friendly interface.
Pricing: Visit the website for detailed pricing
6. Trends Related to Customer Identity and Access Management (CIAM) Software
The Customer Identity Access Management market size is estimated to be USD 14.9 billion in 2024 and is expected to be USD 31 billion in 2032, continuing to grow at a CAGR of 13.03% within the forecast period 2026-2032. The CIAM platform environment is evolving and the new customer demands, as well as emerging technologies, set up the major trends that should be taken into account by every organization.
1. The Rise of Passwordless Authentication
The next frontier of the industry is to move away from the use of passwords altogether. CIAM Technology is quickly embracing such standards as FIDO2/WebAuthn, biometric authentication, and magic links. These practices not only get rid of the most common source of security breaches weak or stolen passwords but also greatly minimize the friction of logging in which improves the customer experience. It is among the most significant changes all CIAM providers have.
2. AI and Machine Learning for Adaptive Security
CIAM solutions are adopting Artificial Intelligence (AI) and Machine Learning (ML) to make real-time and risk-based decisions about access. Rather than a fixed allow or deny system, AI is able to evaluate hundreds of contextual clues (e.g., location, device, behavioral biometrics) to assign a risk score, within which the CIAM software can dynamically challenge high-risk logins with additional authentication, being able to keep everyone secure without frustrating low-risk users
3. Identity Orchestration as a Core Capability
Identity orchestration is the application of a low-code or no-code visual engine to build and operate intricate customer experiences involving in-app and third-party services (such as fraud detection or marketing automation). It has enabled businesses to develop highly personalized, secure, and frictionless flows in a short time without the extensive understanding of a developer; the underlying CIAM identity administration infrastructure has become significantly much more nimble.
4. Decentralized and Verified Identity (Self-Sovereign Identity)
One of the more long-term trends is to revert identity credentials to a customer, commonly supported by blockchain technology. Verified ID and Decentralized Identity (DID) enable the customers to store and manage their own digital credentials (e.g., verified age, employment status) and choose, on their own, with whom to share them with the services. This leaves the enterprise to the side in terms of the burden and risk of data storage, which is a significant possible change of CIAM platforms.
5. Increased Focus on Privacy and Consent Management
The compliance functions of CIAM software are becoming more salient with the global regulations becoming stricter. It is shifting from more than mere opt-in boxes to detailed, granular consent management dashboards and support for privacy API data deletion and explicitly addressing the data sovereignty needs, so the Customer Identity and Access Management Platform is a legal and compliance defense.
7. Conclusion
The choice of Customer Identity and Access Management (CIAM) software is a signature choice in your digital business. The appropriate CIAM solution should not act as a security tool, but it should be a strategic asset. Regardless of whether you choose the developer-oriented nature of Okta, the enterprise-grade scalability of Ping Identity, the ecosystem prowess of Microsoft Entra ID, the extreme versatility of ForgeRock, or the governance prowess of IBM Security, investing in a major CIAM vendor is the key move towards future-proofing your digital infrastructure. It is now time to choose your basic CIAM technology.

 Researched and Written by
Researched and Written by 


