The digital landscape constantly grows and so do the dangers associated with it. Proxy servers have become indispensable tools for security, optimizing performance, and ensuring scalability.
Relevant data for 2023 shows incredible numbers, the global proxy server market was valued at around USD 3.4 billion and is expected to reach USD 7.2 billion by 2031. This basically means it will be growing at a compound annual growth rate (CAGR) of 7.03% . This growth is driven by increasing cybersecurity concerns, the rising demand for online privacy, and the expansion of internet-based services.
Notably, reverse proxy services have seen significant adoption, with Cloudflare alone accounting for 19.4% of all websites, representing a market share of 81% among reverse proxy services . Understanding the multifaceted applications of proxy servers is key for individuals and organizations aiming to bolster their digital infrastructure
Exploring Proxy Servers: Types And Their Applications
So, what do you need a proxy server for? They are mainly used for online security, privacy, and performance. They serve as intermediaries between clients and the internet and offer various functionalities tailored to many different needs.
We will go into the different types of proxy servers and their specific applications. We wanted to give actionable insights for both individuals and organizations.
Types Of Proxy Servers
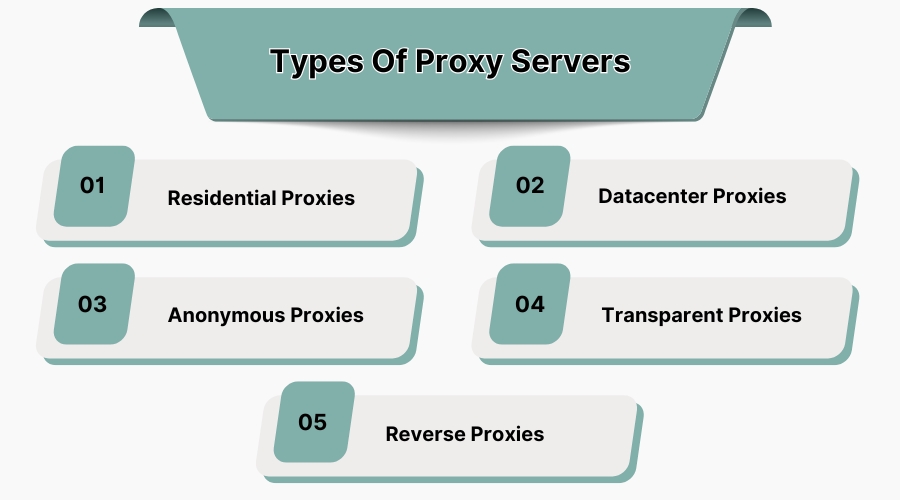
Before you choose the right proxy for you it's necessary to know what the various types of proxies do. This is vital for selecting the right solution to meet specific requirements.
Residential Proxies
Residential proxies are the meat and potatoes of proxies. They work by using IP addresses assigned by Internet Service Providers (ISPs) to homeowners around the world. User traffic gets routed through real residential IPs, making online activities appear as though they originate from other parts of the world. This authenticity reduces the likelihood of being blocked or flagged by websites that are geo locked.
Applications
-
Market Research and Data Collection: Businesses with residential proxies can get data from websites without detection, ensuring access to accurate and precise information.
-
Accessing Geo-Restricted Content: Users can bypass regional restrictions to access content or services available only in specific countries.
-
Ad Verification: Companies use residential proxies to verify that their advertisements are displayed correctly across different regions and platforms
Considerations
Residential proxies offer anonymity and reliability, but they are typically more expensive than other proxy types due to their legitimacy and lower risk of detection.
Datacenter Proxies
Datacenter proxies are not affiliated with ISPs but are provided by third-party organizations through data centers. The connections are high-speed and cost-effective, great for tasks that require rapid data retrieval.
Applications
-
Bulk Data Scraping: Ideal for extracting large volumes of data where speed is key, and the risk of IP bans is minimal.
-
Automated Testing: Used in testing applications or websites by simulating multiple user accesses without geographical constraints.
Considerations
Since datacenter IPs can be easily identified, they are more susceptible to blocking by websites compared to residential proxies.
Anonymous Proxies
Anonymous proxies hide the user's IP address and present themselves as proxies without revealing the IP. This provides much in terms of anonymity, making it harder for target websites to track the user's online activities.
Applications
-
Enhanced Privacy Browsing: Individuals use anonymous proxies to prevent websites from tracking their browsing habits.
-
Bypassing IP-Based Restrictions: Access content or services that restrict users based on their IP addresses.
Considerations
While they offer anonymity, the level of privacy may vary, and they might not encrypt traffic, leaving data potentially vulnerable.
Transparent Proxies
Transparent proxies inform websites of their presence and forward the original IP address to the web server. They are typically used for content filtering and monitoring purposes.
Applications
-
Content Filtering: Organizations and educational institutions use transparent proxies to monitor and restrict access to inappropriate or non-work-related websites. Among other things, this means no NSFW content.
-
Caching Frequently Accessed Content: Improves load times and reduces bandwidth usage by storing copies of frequently accessed resources.
Considerations
Since transparent proxies do not provide anonymity, they are not suitable for users seeking to hide their IP addresses.
Reverse Proxies
Reverse proxies are at the forefront of web servers and handle incoming client requests, distributing them to multiple backend servers. This setup is the one organizations should watch out for since it enhances security, load balancing, and scalability.
Applications
-
Load Balancing: Distributes client requests across several servers which means no single server gets overwhelmed.
-
SSL Termination: Both SSL encryption and decryption get managed, reducing the processing load on backend servers.
-
Protection Against DDoS Attacks: Shields backend servers from direct exposure to potential threats by filtering malicious traffic.
Considerations
Implementing reverse proxies can significantly enhance the resilience and efficiency of web services.
Enhancing Security With Proxy Servers
 (11).jpg)
Proxy servers bolster network security by being intermediaries that manage and control traffic between users and the internet - but, we've already covered this. Let us now dig deeper into how they work to improve safety.
Strategies
-
IP Masking and Anonymity: By routing internet traffic through a proxy, users can conceal their real IP addresses. Malicious entities can't target you if they don't know where you are.
-
Content Filtering: Proxies can be configured to your heart's content to block access to malicious websites, preventing phishing attacks and unintentional malware downloads.
-
Access Control: Organizations can use proxies for access policies, so only authorized users can access specific data.
Actionable Advice
-
Regularly Update Proxy Configurations: Ensure that proxy servers are configured correctly and updated regularly to protect against emerging threats.
-
Combine Proxies with Firewalls: Integrate proxy servers with firewall systems to create a security infrastructure that monitors and controls incoming and outgoing traffic.
Maximizing Business Efficiency: How Proxy Servers Enhance Network Speed
Now let's dive into how proxies help internet speed. It's pretty much apocryphal but network speed is a factor sine qua non for operational efficiency, customer satisfaction, and overall business performance.
How do proxy servers factor into this? They are needed for optimizing speed, reducing latency, and ensuring data flow—key. Let's look at two key factors below.
Accelerating Data Access Through Caching
Proxy servers can store cached versions of frequently accessed web resources, including websites, images, and applications. When employees or customers request this content, the proxy delivers it directly from its cache, meaning no communication with the original server happens.
What does that mean? Much shorter load times and less bandwidth consumption, resulting in faster, more efficient workflows.
Reducing Bandwidth Costs with Data Compression
Data gets compressed before transmission, and then proxy servers minimize the volume of information transferred over the network.
This is of particular use for businesses with global operations, where reducing data size can significantly lower bandwidth costs while enhancing download and upload speeds. Faster data flow contributes to improved communication, rapid project delivery, and smoother customer interactions.
Enhancing Business Scalability Through Advanced Proxy Server Implementations
Proxies significantly contribute to business scalability through several many functions but we have decided to highlight two you will find below. However, we have consciously decided not to mention load bearing and data compression here since they have already been covered above. You already know what they do, and it helps scalability as well - would be the “too long didn’t read” of those sections.
Content Caching and Bandwidth Optimization
Proxy servers can cache frequently accessed content, reducing the need to retrieve data from the origin server repeatedly. This caching mechanism not only decreases latency but also optimizes bandwidth usage, allowing businesses to handle increased traffic without proportional increases in infrastructure. By minimizing redundant data transfers, proxies enhance the efficiency of network resources, supporting scalable growth.
SSL Termination and Load Distribution
Implementing SSL termination proxies enables the offloading of SSL encryption and decryption processes from backend servers. This offloading does away with the computational burden on application servers, allowing them to handle more user requests. When combined with load balancing (of which you should be an expert by now), SSL termination proxies distribute incoming traffic evenly across multiple servers, preventing overloads and ensuring consistent performance as demand scales.
Wrapping Up
Even though we've given only a short overview of the types of proxies there are and how they work to secure your life and business, help you out with internet connection speed and scalability (definitely for business) we believe have clearly outlined their necessity for the digital age. Further advancements can be expected as proxy servers continue to evolve with artificial intelligence and machine learning. Let’s face it - these advancements are expected in pretty much every field there is and proxy servers, being a digital age thing, can be no exception. Looking ahead in a general manner, the growing demand for decentralized and blockchain-based proxies may further redefine internet privacy and security landscapes.
Proxies act as intermediaries between your device and the internet, hiding your IP address and adding a layer of security. They protect data by filtering malicious content and blocking unwanted connections.
Yes, caching proxies store frequently accessed data, reducing the time needed to fetch information and speeding up browsing. Some proxies also compress data to optimize bandwidth.
Proxies distribute network traffic across multiple servers, preventing overload and ensuring smooth performance, making them essential for scalable network management.
Residential proxies offer high anonymity, while data center proxies deliver faster speeds. Reverse proxies are great for load balancing and hiding backend servers.