Pricing of Marg ERP-Pharmaceutical Industry Software
Pricing plans
Introduce pricing plans
Simple, transparent pricing that grows with you. Try any plan free for 30 days.
Click here to get detailed pricing as per your requirements.
Key Specification
| Other Categories: | |
|---|---|
| Deployment: | Cloud Hosted,Hybrid,Any |
| Customer Support: | Phone,Email,Live Chat |
| Customization: | No |
| Languages Support: | English |
Who uses Google Cloud Key Management Service




Company Details
- Company Name: Google
- Headquarter: California United States
Google Cloud Key Management Service Description
Google Cloud Key Management Service (KMS) provides centralized, cloud-native control over cryptographic keys for protecting data across Google Cloud and custom applications. The platform offers flexible options to meet diverse security requirements, whether keys are stored in Google’s infrastructure, backed by dedicated hardware modules, or maintained externally under customer control.
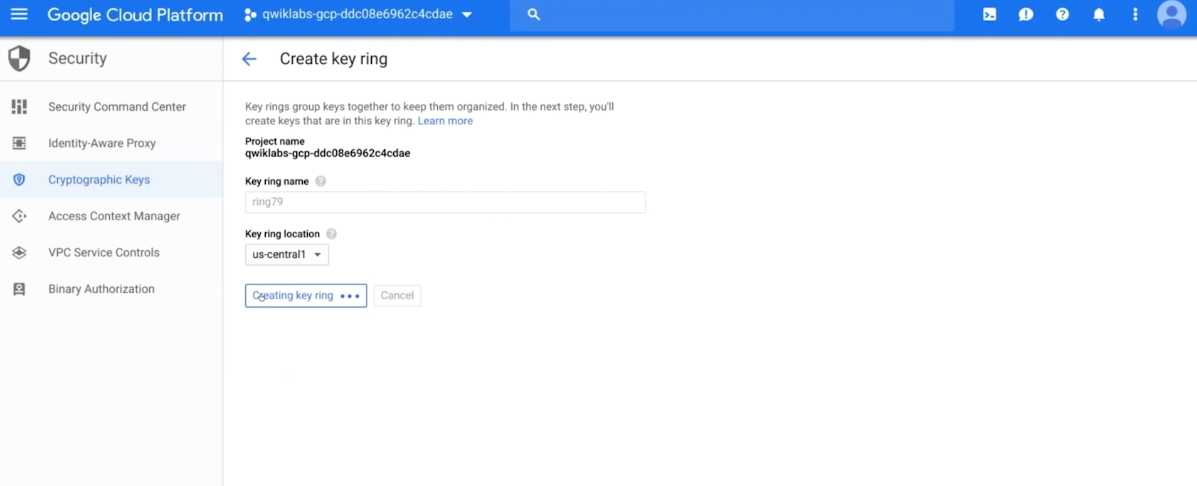
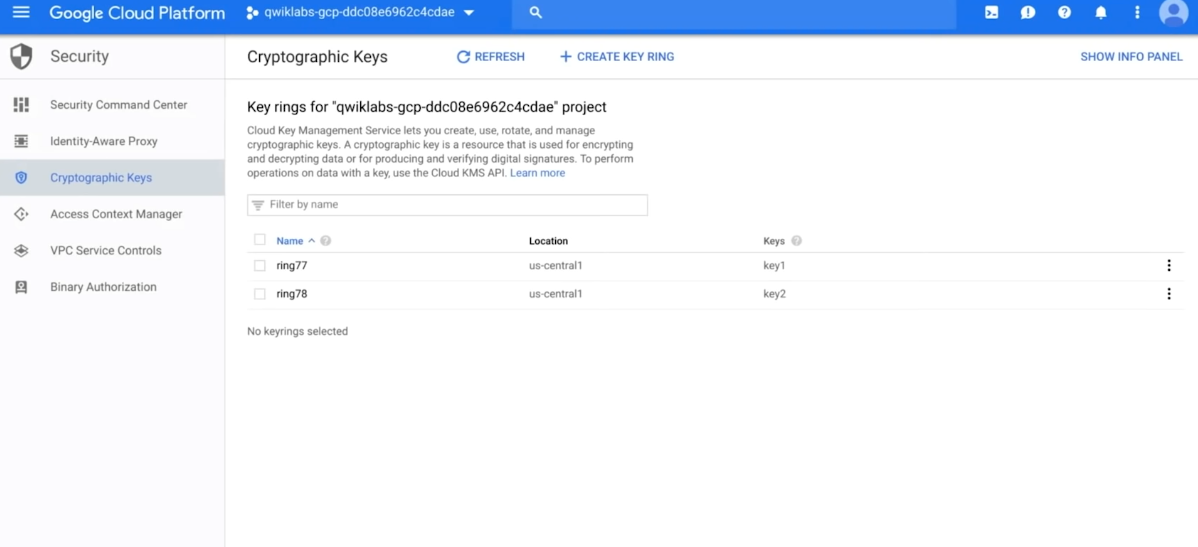
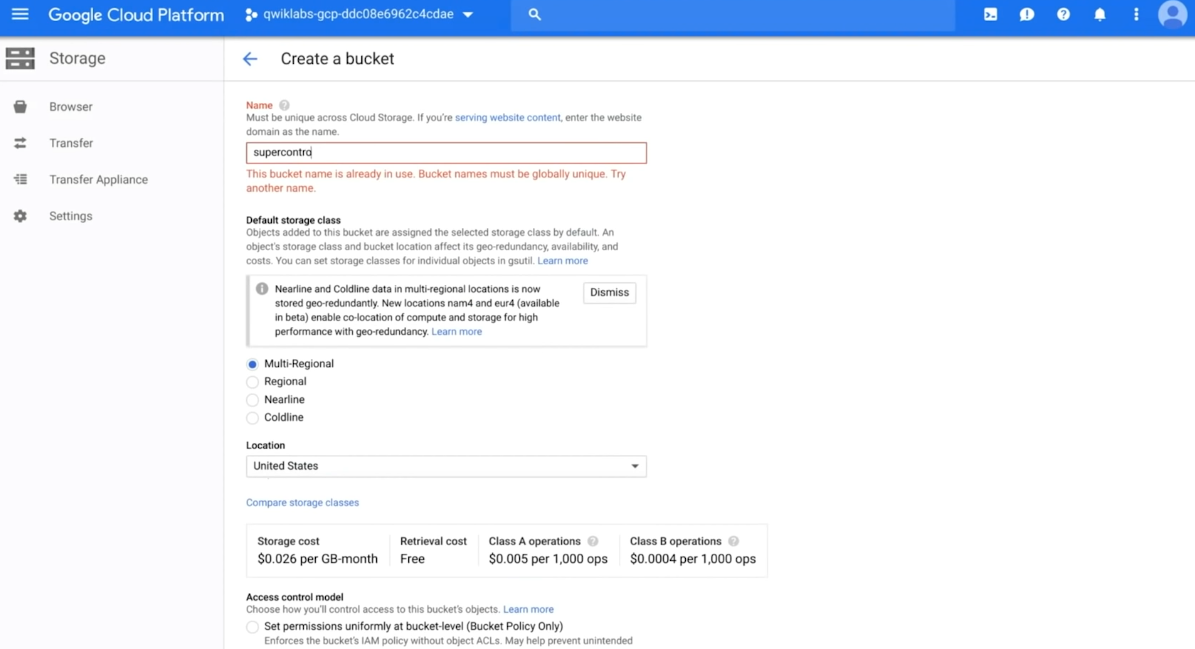
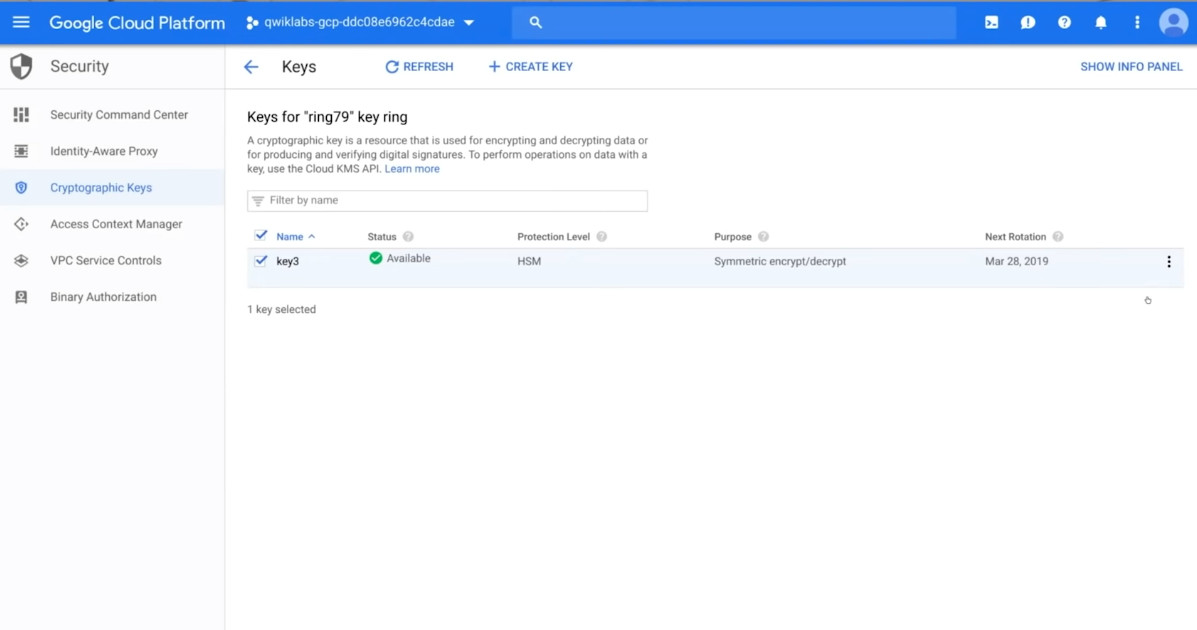
Keys are organized into key rings scoped by project and region, enabling data locality and policy separation. Supported algorithms include AES-256 for symmetric encryption, and RSA and elliptic curve options for asymmetric encryption and digital signatures. Key operations—encryption, decryption, signing, and MAC validation—are available through API calls and SDKs.
KMS includes full lifecycle management: keys can be generated, imported, versioned, automatically rotated, and securely destroyed. Envelope encryption is built-in to support scalable protection of large datasets by using data keys protected under master keys. IAM-based role controls manage access at the key or key ring level, while detailed Cloud Audit Logs ensure visibility into all operations.
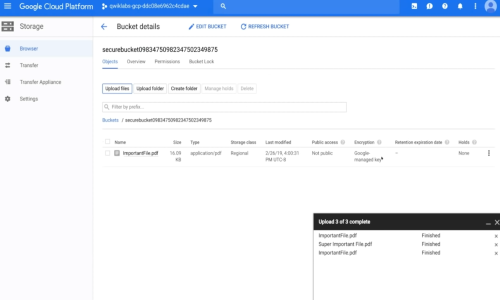
This flexible architecture allows organizations to meet security, compliance, and sovereignty requirements. Integrations with services like BigQuery, Secret Manager, and Compute Engine make it simple to implement encryption across storage, compute, and data analytics platforms.
Auditability, compliance alignment, and automation capabilities make Cloud KMS ideal for regulated sectors such as finance, healthcare, and public services. It enables seamless global key replication, redundancy, and high availability through Google’s infrastructure.
In summary, Google Cloud KMS delivers robust, policy-enforced cryptographic operations that are secure, scalable, and compliant—suiting enterprises seeking control, agility, and resilience in their encryption strategies.
Key Features
Support for Multiple Key Types: Symmetric (AES-256) and Asymmetric (RSA 2048/3072/4096, EC P256/P384) key algorithms.
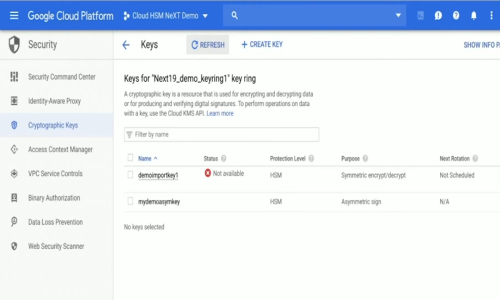
Protection Levels: Choose between software-backed keys, hardware-backed (Cloud HSM – FIPS 140-2 Level 3), or External Key Manager (EKM) where keys stay outside Google Cloud.
Full Key Lifecycle Management: Key generation, import, rotation, versioning, deactivation, destruction, and scheduled operations.
Envelope Encryption: Enables scalable encryption by wrapping data keys with master keys (KEKs).
IAM-Based Access Control: Granular permissions at the key and key ring levels using Identity and Access Management (IAM).
Cloud Audit Logging: Comprehensive logging of all cryptographic operations for compliance and monitoring.
Service Integrations: Natively integrates with Google Cloud services like BigQuery, Cloud Storage, Compute Engine, and Secret Manager.
Digital Signing and Verification: Supports asymmetric key operations for signing and verifying digital data.
Global Availability & Scalability: Region-specific key rings with high availability, replication, and redundancy.
Compliance Ready: Meets standards such as FIPS 140-2, GDPR, HIPAA, and PCI DSS.
Secure API Access: REST API and client libraries for key operations in development workflows.
External Key Manager (EKM): Maintain full key custody and sovereignty with off-cloud key storage.
Cloud HSM: Managed hardware security module offering high-assurance protection without hardware management overhead.
Key Access Justifications: Provides transparency and control over key access attempts by Google.
Automated Operations: Supports automated key rotation and usage policy enforcement.
Key Features & Specifications
- Data Security
- Network Security
- Threat Response
- Web-Application Security
- Anomaly/Malware Detection
- Access Controls/Permissions
- Threat Intelligence
- Master Key Management
- Keyword Analysis
- Keyword Rank Tracking
- Network Access Control
- Cloud Security
Google Cloud Key Management Service Video
Alternative
More AlternativeUser Reviews
WRITE A REVIEWKeka HR Payroll Platform Key Clients
Frequently asked questions
Everything you need to know about discovering, comparing, and choosing the right AI software for your business.
Google Cloud Key Management Service has 0 plans.
Google Cloud Key Management Service is the AI Key Management Software used for the below functionalities.
Top 5 Google Cloud Key Management Service features
- Data Security
- Network Security
- Threat Response
- Web-Application Security
- Anomaly/Malware Detection
Google Cloud Key Management Service provides Phone,Email,Live Chat support.
Google Cloud Key Management Service is not allowing Free Trial.
Google Cloud Key Management Service provides Help Guides,Video Guides,Blogs,Webinars,Case Studies,Whitepapers for the software training.
Need Help Selecting
the Right AI Solution?
Speak with our team for tailored recommendations and insights to accelerate your AI adoption.