Pricing of Marg ERP-Pharmaceutical Industry Software
Pricing plans
Introduce pricing plans
Simple, transparent pricing that grows with you. Try any plan free for 30 days.
BeyondTrust Endpoint Privilege Management
USD 0.00 /
USD0.00
Perfect for your business requirements and platform usage.
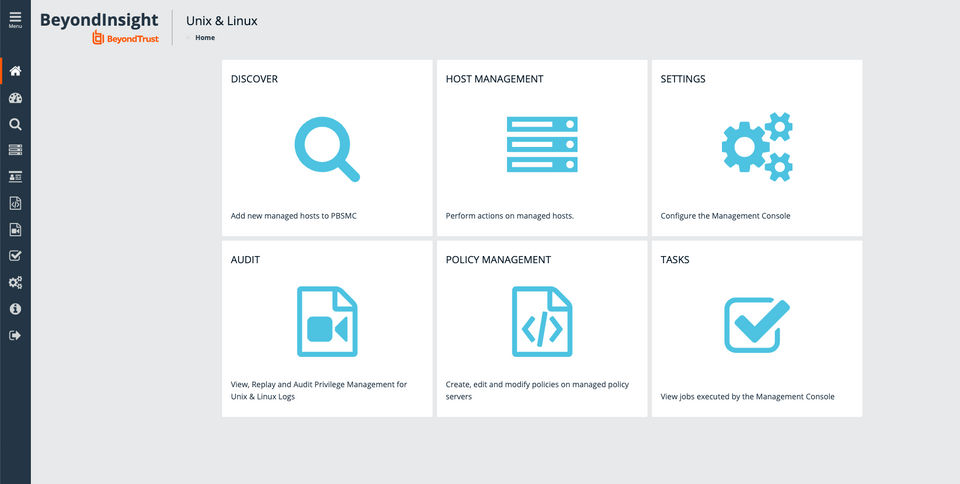
BOOK A DEMO- Auditing and Governance
- Fine Grained Least Privilege
- Remote System App Control
- Dynamic Access Policy
- File and Policy Integrity Monitoring
- Threat Reporting and Analytics
- Improved Efficiency
- Easier Compliance
- Enhanced Security
- Auditing and Governance
- Fine Grained Least Privilege
- Remote System App Control
- Dynamic Access Policy
- File and Policy Integrity Monitoring
- Threat Reporting and Analytics
- Improved Efficiency
- Easier Compliance
- Enhanced Security
Key Specification
| Other Categories: | |
|---|---|
| Deployment: | Cloud Hosted |
| Customer Support: | Online (Ticket) |
| Customization: | No |
| Languages Support: | English |
Who uses BeyondTrust Endpoint Privilege Management


Company Details
- Company Name: BeyondTrust Endpoint Privilege Management
- Headquarter: Johns Creek,
BeyondTrust Endpoint Privilege Management Description
Who Uses BeyondTrust Endpoint Privilege Management?
BeyondTrust Endpoint Privilege Management is used by:
-
Medium to large enterprises
-
IT security teams
-
Regulated industries such as finance and healthcare
-
Government and public sector organizations
-
Businesses with distributed endpoint environments
It is ideal for organizations focused on endpoint security and compliance.
Why Choose BeyondTrust Endpoint Privilege Management?
Organizations choose BeyondTrust for its proven approach to reducing attack surfaces while maintaining operational efficiency. As a trusted BeyondTrust privilege manager, it offers granular control over user privileges, strong auditing capabilities, and enterprise-grade scalability.
Benefits of BeyondTrust Endpoint Privilege Management
-
Reduces risk by eliminating unnecessary admin privileges
-
Protects endpoints from malware and ransomware
-
Improves compliance with security standards
-
Enhances visibility into privileged activities
-
Maintains user productivity without disruption
-
Centralized control across endpoints
These benefits make it a reliable privilege management app for enterprise security teams.
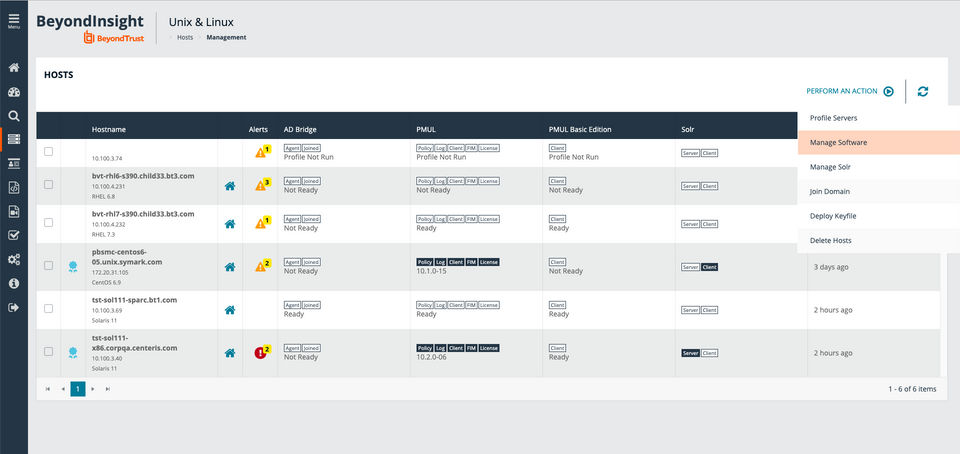
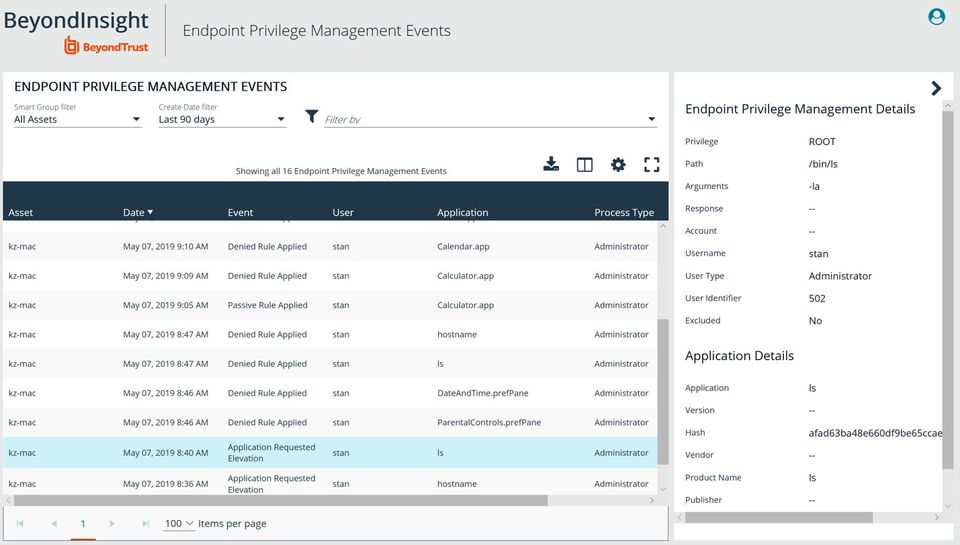
Features of BeyondTrust Endpoint Privilege Management
Key features include:
-
Least-privilege policy enforcement
-
Application control and elevation management
-
Endpoint activity monitoring and auditing
-
Role-based access and approval workflows
-
Integration with existing security tools
-
Centralized management console
These features position BeyondTrust endpoint privilege management as a robust enterprise solution.
How to Use BeyondTrust Endpoint Privilege Management?
To use BeyondTrust Endpoint Privilege Management:
-
Deploy the agent across endpoints
-
Define privilege and access policies
-
Remove local admin rights where unnecessary
-
Monitor privileged activities in real time
-
Review reports for audits and compliance
The platform is designed for smooth deployment and ongoing management.
BeyondTrust Endpoint Privilege Management Demo
BeyondTrust offers a demo experience that allows organizations to explore how BeyondTrust EPM manages privileges, enforces policies, and monitors endpoint activity. This helps teams evaluate its fit within their security framework before implementation.
BeyondTrust Endpoint Privilege Management Pricing
BeyondTrust endpoint privilege management pricing typically depends on the number of endpoints, deployment type, and feature requirements. Pricing is tailored for enterprise needs, making it scalable for organizations of different sizes while supporting long-term security goals.
BeyondTrust Endpoint Privilege Management Review
Users consistently highlight strong security controls, detailed reporting, and reliable policy enforcement in reviews of BeyondTrust. The BeyondTrust privilege manager is widely regarded as an effective solution for reducing endpoint-based threats and strengthening overall security posture.
BeyondTrust Endpoint Privilege Management Video
Alternative
More AlternativeUser Reviews
WRITE A REVIEW
What do you like best?
The software keeps your computer secure I guess. One of the problems I have is it's a super strict version of User Account Control which comes with Windows. It gives you options to explain why you're installing a piece of software.
What do you dislike?
It's super super strict. I guess it's security software so that's to be expected but there were times I couldn't install software and that was quite annoying in lost productivity.
Recommendations to others considering the product:
It's decently good security software if you're trying to keep systems extremely secure.
What problems are you solving with the product? What benefits have you realized?
Security. Benefits are that I've not had my machine infected with malware at all.

What do you like best?
It's the easiest and most efficient solution for any IT manager. I've had the best experience, and I've noticed that not only can you easily support nearly any person on your network, but you can also even allow external members if needed. Another aspect that I like uniquely is being able to display that an unauthorized person can see your device. This can be used for educational purposes. The recording will often be helpful. It's pretty much easy to set up. Although there are a lot of rivals out there, I'd still go for beyond trust.
What do you dislike?
There are just a few drawbacks that I have, but they're very minimal. One is that they're not yet in a position to support Chrome OS, and it seems like they're behind the competition here. The other con is downloading the updates on your host device in your cloud storage. The fixing process might use more consideration to the skill of the user or someone not as skilled in networking, etc.
What problems are you solving with the product? What benefits have you realized?
Overall, this has been a wonderful tool that helps you to have IT support at your side as if you had someone placed right beside you. I used it to provide virtual customer service to people in virtual workplaces, home offices, and remote traveling. And it also helped me analyze the market, prepare staff to use it, and manage department customers before product extension as an enterprise-wide primary approach.

What do you like best?
that we don't have to give administrator rights to every user that needs to just install software on their machine. Their support is great and has been able to solve all our problems in a timely manner. We can also give admin rights to open certain files. like open the host file, tns file for databases, etc.
What do you dislike?
It can get complicated when you have many rules. Right now we are 2 years into using the software and have many rules. You need to make sure you title the rules well in order to differentiate them
Recommendations to others considering the product:
Make sure you try the produc tand see if it makes sense for your situation. Take your time, and make sure you talk to all departments that will be using this to make sure you can write the rules accordingly.
What problems are you solving with the product? What benefits have you realized?
we used to give everyone who needed to install software full local administrator rights to their machine. This was posing a security risk where if their account was compromised they could get rights to that workstation. With this software we are able to inject admin rights when people needed by writing rules that match certain criteria (path, hash etc) and people can still get work done, install software, but they do not have full administrator rights.

What do you like best?
Gives lot of control to the System Admistrators and Desktop Sucurity teams.
It is user friendly and easy for monitoring as what your Users can install/run with elevated privileges.
What do you dislike?
Sometimes the interface is confusing and need luser education as a user you need to know the process to use it.
What problems are you solving with the product? What benefits have you realized?
It gives the System Admins to provide elevated permissions thorough the Avecto Tools and access management made easy.

What do you like best?
Avecto seems to do a pretty good job of not allowing users to access unapproved material through the company I work for.
What do you dislike?
When updates or scans are running in the background, it tends to slow the processing speeds way down.
What problems are you solving with the product? What benefits have you realized?
Helps protect the company from users accessing sites prohibited by DHHS.
Keka HR Payroll Platform Key Clients
Frequently asked questions
Everything you need to know about discovering, comparing, and choosing the right AI software for your business.
BeyondTrust Endpoint Privilege Management has 1 plans,
- BeyondTrust Endpoint Privilege Management USD 0.00
BeyondTrust Endpoint Privilege Management provides Online (Ticket) support.
BeyondTrust Endpoint Privilege Management is not allowing Free Trial.
BeyondTrust Endpoint Privilege Management provides Help Guides,Blogs for the software training.
Need Help Selecting
the Right AI Solution?
Speak with our team for tailored recommendations and insights to accelerate your AI adoption.